GDPR compliance & ITSM: Is your IT service management system ready?
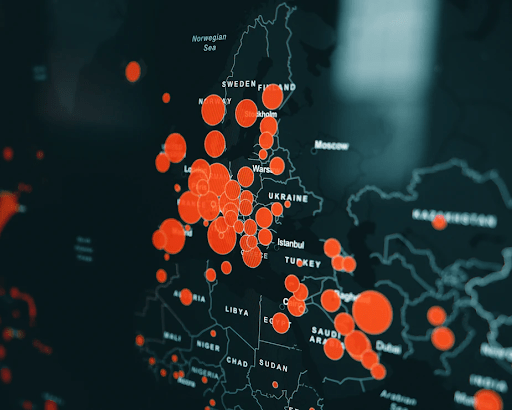
The General Data Protection Regulation (GDPR) went into effect in May 2018. This comprehensive new set of rules is intended to protect the private information of European Union (EU) citizens, wherever they are in the world. This has significant implications for any company that does business with EU citizens, wherever that company is located. Personal Identifiable Information (PII) denotes sensitive data with potential privacy and security implications.
The Penalties in 2019
Every EU member state has a Data Processing Authority (DPA) responsible for enforcing GDPR. Businesses are expected to self-report breaches that could threaten EU PII to their DPA within 72 hours of discovering the breach.
The DPA for the United Kingdom (UK) is the Information Commissioner’s Office (ICO). In April 2018, the month before GDPR took effect, the ICO received reports of 367 breaches. In June, the first full month after GDPR took effect, the ICO received 1,792 such reports.
Not all breaches are GDPR violations, but some are very likely to be. And with violations will come fines, bans, and reputational damage. Great reasons to minimize breaches and maximize PII control, security, and transparency at your business.
Preparing for GDPR compliance
It almost doesn’t matter whether your business is a GDPR controller, processor, or both. GDPR still represents a clarion call to all IT decision-makers to devote serious attention to knowing where, when, and why PII traverses any part of their business’ IT estate.
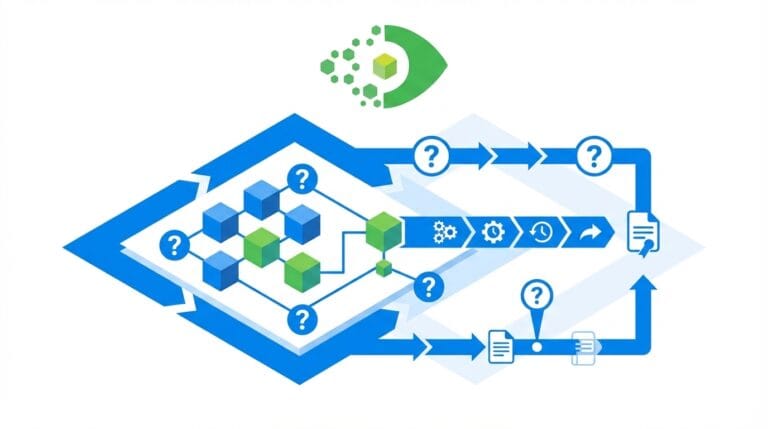
The knowledge you need starts with whatever your business knows about the core of its IT infrastructure. This includes your endpoint devices, your servers, your cloud-based services, and your most critical applications. You also need to be able to map and track the interconnections that link all of those elements to one another and to your users.
To achieve and maintain the knowledge you need, you need four enablers – effective IT Asset Management (ITAM), IT Service Management (ITSM), a Configuration Management Database (CMDB), and interoperability among all three. Your ITAM and ITSM solutions can map and track what’s in your IT infrastructure. The CMDB is your key to mapping and tracking the relationships among your infrastructure elements and users.
(See, “Why You Can’t – and Shouldn’t – Spell “GDPR” without “ITAM””)
All of these solutions must also be closely harmonized with cyber security initiatives at your business. (A recent webinar co-hosted by Virima and follow-up addresses the bringing together of IT and cyber security operations and management in detail.)
Achieving GDPR compliance is just the latest high-profile effort to protect PII and punish those who fail to do so. More such regulations are coming – during and beyond 2019.
Protection for your business begins with the technologies and processes that govern its IT and cyber security operations. If your business hasn’t yet begun pursuing ITAM, ITSM, or CMDB deployment, it may now have sufficient inducement to do so.
Get Your IT Management “GDPR-ready” With Virima
Virima’s solutions for IT Asset Management (ITAM) and IT Service Management (ITSM) can help you protect the PII of your customers and users, and your company. Virima solutions can automatically discover and map your critical IT resources and the interconnections that link them to one another, your applications and services, and your users.
In addition, they’re built to be easy to use and configure, and to produce useful, actionable reports about your IT environment, for IT managers and business decision makers.
Virima features can automatically discover and map your critical IT resources and the interconnections that link them to one another, your applications and services, and your users.
Virima is here to help. To get started, contact us today to schedule a demo and explore the possibilities!