Integrating SecOps With Your ITSM: How to Get Started (Part 2)
IT Service Management (ITSM) and Security Operations (SecOps) are equally critical to survival and success at many businesses. Also, the need to bring them closer together and how best to accomplish that goal were among the topics discussed in a recent webinar hosted by Virima.
The featured presenters were Taylor Lehman and Mike Bombard. Taylor is Chief Information Security Officer for Wellforce (a partnership of Tufts Medical Center and Floating Hospital for Children), MelroseWakefield Healthcare, and Circle Health in Massachusetts. Mike Bombard is Virima’s Chief Operating Officer.
The first part of this two-part post discussed why ITSM and SecOps must come together, the drivers for their evolution, and some useful first steps toward their convergence. Additionally, this time, address specific challenges to enablers of ITSM-SecOps convergence, and consider the next steps you can take to bring them together at your business.
ITSM-SecOps Convergence: Challenges
Every IT and business initiative faces multiple challenges. Also, bringing ITSM and SecOps together is no exception. Broadly, the most significant of these challenges fall into three categories: organizational, technological, and cultural.
Below are just some of the challenges your business is likely to face when trying to bring ITSM and SecOps together.
Organizational Challenges
- Do we have the required workforce?
- Are they assigned to adequate roles?
- How do we eliminate silos of information?
ITSM-SecOps Convergence: Technological Challenges
- Do we have contingencies in place?
- Can we procure what is required and unavailable?
- Do we have the skills to achieve our objectives?
Cultural Challenges
- Does our leadership understand why this is important for business?
- Do we have the right framework and processes in place to see it to success?
- Can we bridge the cultural gaps to ensure a smooth integration journey?
ITSM-SecOps Convergence: Enablers
Enablers of ITSM-SecOps Convergence can generally be grouped into the same categories as the challenges outlined above.
Organizational Enablers
- Leadership buy-in
- Adequate budget
- Clear goals and solid plans
ITSM-SecOps Convergence: Technological Enablers
- A business-aligned service catalogue
- A comprehensive, flexible, CMDB
- Process-driven automation
- Actionable, role-specific reporting
Cultural Enablers
- Regular cross-functional team meetings
- Well-defined, well-documented, well-enforced business processes
- Acknowledgement, recognition, and rewards
ITSM-SecOps: Next Steps
Once you have crafted a strategy and a plan for ITSM-SecOps convergence, you must take the first steps described in Part 1 of this post. Also, you must know your environment, optimize your skills, get executive support, and engage your stakeholders regularly.
After you complete those first steps successfully, it’s time to shift your focus from high-level strategy to specific tactics. Your specific actions may vary in execution, but each project must at least address the steps outlined below.
Identify a Promising Opportunity
Pick a specific business challenge or opportunity that a better convergence of ITSM and SecOps can help to address.
Devise a Specific Project Plan
Ensure that the tactics and outcomes delineated in the project plan align with both business goals and the larger aims of your plan for ITSM-SecOps convergence.
Engage Your Teams
Identify and get the commitment of the people you need to succeed, and ensure they are kept informed of everything they need to know as the project proceeds.
Pursue The Plan
Make sure it includes regular check-in opportunities and frequent communication, to keep everyone on schedule and to identify and address challenges as quickly as possible.
Distill and Disseminate the Results
Whether reality conforms to plan or deviates from it, make sure the key points of the effort and its results are shared with all stakeholders.
Capture and Store All Relevant Data
What you learn and experience must inform future ITSM-SecOps convergence efforts. If you don’t have an appropriate repository and supporting processes, use your first ITSM-SecOps convergence project as a spur to create them.
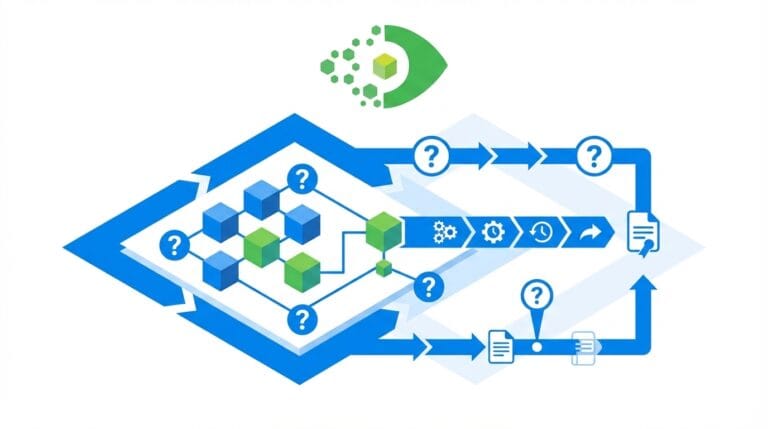
In many cases, that repository should be a configuration management database or CMDB. To maximize your ability to capture all relevant data, ensure that you implement comprehensive, automated IT discovery across your entire IT estate. You also need consistent, reliable automated updating of your CMDB.
(See, “A CMDB without Discovery is just a database”)
These crucial automation steps will help guarantee that your IT and SecOps teams have accurate, complete, and timely information to work from when pursuing ITSM-SecOps convergence.
The webinar features insightful discussions and practical observations to help you explore and advance ITSM-SecOps convergence within your business. Listen to or download the full webinar to gain valuable insights.
Virima features can automatically discover and map your critical IT resources and the interconnections that link them to one another, your applications and services, and your users.
Virima is here to help. To get started, contact us today to schedule a demo and explore the possibilities!