Integrating SecOps With Your ITSM: How to Get Started (Part 1)
IT Service Management (ITSM) and Security Operations (SecOps) are equally critical to survival and success for many businesses. The need to bring them closer together and how best to accomplish that goal were among the topics discussed in a recent webinar co-hosted by Virima.
The featured presenters were Taylor Lehman and Mike Bombard. Taylor is Chief Information Security Officer for Wellforce, MelroseWakefield Healthcare, and Circle Health in Massachusetts. Mike Bombard is Virima’s Chief Operating Officer. This post summarizes some of the points discussed during that event.
ITSM + SecOps: Why They Must Come Together
Both ITSM and SecOps are growing in importance to business operations, success, and growth. Almost every business interaction and transaction relies on some form of IT. And every IT service and estate needs the best possible security.
As IT environments grow in size and complexity, they also become more challenging to secure. Yet effective cyber security is essential if IT is to support business growth and digital transformation initiatives. Anything less places the business and its reputation at significant risk.
Bringing ITSM and SecOps together can enable and accelerate development. and delivery of secure, high-value, IT-powered services. Convergence of ITSM and SecOps can also increase alignment of IT and security initiatives with business needs and goals. Such convergence can also reduce operational and reputational risk, and effectively support business growth and digital transformation.
At some businesses, so-called “disruptive technologies,” including Artificial Intelligence (AI), Machine Learning (ML), Big Data, and the Internet of Things (IoT), are driving efforts to improve ITSM. At some businesses, ITSM improvement is part of a larger push toward Digital Transformation.
Meanwhile, additional drivers spur pursuit of SecOps. These drivers include the need to eliminate silos of information and the desire to automate repetitive security and IT tasks. Another is the continuing evolution of successful cyber security threats, from phishing emails to malware as a service.
At every business, however, there is a common driver of evolution for both ITSM and SecOps. That is the increasing business criticality of IT-powered services and the technologies that enable them. The more essential these services and technologies become, the more important it is to optimize service development, delivery, and management and maximize security.
Against this backdrop, bringing ITSM and SecOps closer together can be an important step in the evolution of IT management and your business as a whole.
ITSM + SecOps: First Steps
To begin or accelerate efforts to converge ITSM and SecOps, you must first understand that waiting and hoping is not a strategy or a plan. Each must be thoughtfully considered, clearly documented, and focused on business outcomes.
Here are some initial steps toward that strategy and plan.
Know Your Environment
You can’t manage, converge, or optimize what you don’t know about and can’t see. This includes all your critical assets and the connections and relationships that link them to each other, your services, and your users.
You also need to know about every new connection and request for access, and be able to deliver consumable and actionable information about your environment to all who need it.
Optimize Your Skills
Before you start trying to bring ITSM and SecOps together, make sure you have no serious skills gaps that could trip you up later. Make an honest assessment, and do your best to fill any gaps you do find, internally or with outside help. And automate everything you can, to extend the reach of the skilled people you do have.
(See, “Intelligent Automation: the solution to your IT skills shortage”)
Get Executive Support
Make the strongest business case you can. Focus on relevant business outcomes and metrics, and connect improved ITSM and SecOps to these. Keep your supporters and sponsors informed and happy.
Executive sponsorship and support can provide the pull you need to see your ITSM-SecOps convergence initiatives succeed.
Communicate, Validate and Enforce
Identify and keep in touch with all of your stakeholders. Tell them what you’re doing, what you’re going to do, what’s going to happen, how it’s going to help them and the business.
The second part will focus on specific challenges to the enablers of ITSM-SecOps convergence. It will also recommend specific steps to guide you forward.
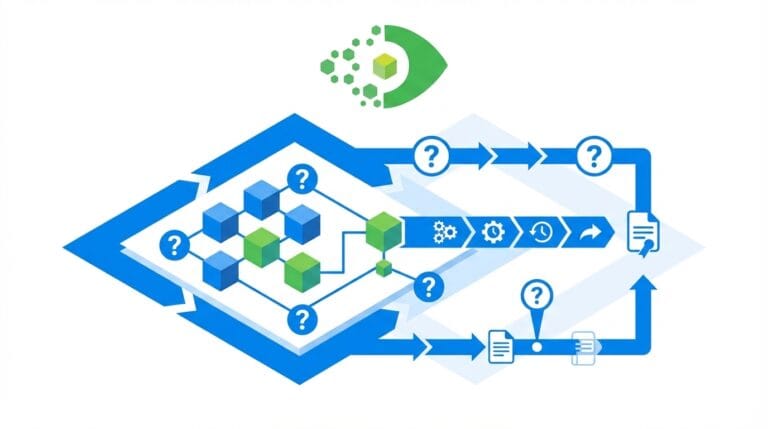
Virima features can automatically discover and map your critical IT resources and the interconnections that link them to one another, your applications and services, and your users.
Virima is here to help. To get started, contact us today to schedule a demo and explore the possibilities!