Crafting a Robust Cybersecurity Response Plan: Is Your Business Prepared?
The gap between IT Service Management (ITSM) Security and a comprehensive cybersecurity strategy represents a critical challenge, impacting the speed and effectiveness of threat mitigation and compromising the robustness of the overall cybersecurity response plan.
CompTIA, a leading IT industry membership association, has published its IT Industry Outlook 2018 report. That study cites IDC research that projects, “global information technology spending will top $4.8 trillion in 2018, with the U.S. accounting for approximately $1.5 trillion of the market.”
A survey of IT professionals conducted for the 2018 New York Tech Summit found that 85 percent of respondents spend up to half their total IT budgets on security-related investments. This only makes sense. In the 2017 edition of this survey, nearly half the respondents (49%) cited security as their top concern.
Given those concerns and spending patterns, cybersecurity spending in 2018 could be as high as $.75 trillion in the U.S. and $2.4 trillion worldwide. Yet, no level of spending guarantees sufficient protection for your business against every threat or attack.
The need for a cybersecurity response plan: Cybersecurity Threats Continue to Grow and Evolve
That’s because the threats to cybersecurity at your business are growing in number, sophistication, and impact. A May 2018 Marketwatch article cited research by the Identity Theft Resource Center, a U.S. non-profit. That group found the number of “significant breaches at U.S. businesses, government agencies, and other organizations topped 1,300,” compared with fewer than 200 in 2005.
Phishing emails and websites are gaining greater personalization and persuasion features. In October 2018, the independent Anti-Phishing Working Group (APWG), reported detection of more than 230,000 unique phishing websites during the second quarter of the year. Each of these sites can have hundreds or thousands of URLs that direct unwitting victims to them.
During that same quarter, APWG members reported more than 280,000 unique email phishing campaigns. Payment processors bore the brunt of over one-third (36%) of those attacks, and software as a service (SaaS) and webmail providers faced over one-fifth (21%).
And so-called business email compromise or BEC attacks now often contain names and specific information that increase their perceived legitimacy. That information is frequently gathered from social media sites.
Meanwhile, malware as a service continues to grow. This threat is particularly insidious. It enables criminals with no technical skills to pay a fee to have a selected number of computers infected with ransomware or other dangerous code.
(See, “Strengthen your defenses against phishing, botnets, and other cyber threats”)
Cybersecurity Threats: The Best Cybersecurity Response Plan
Whatever the number and mix of threats your business faces, you must be ready. You IT and cybersecurity leaders, teams, solutions, and processes must be agile to face them effectively. This means you need the ability to discover vulnerabilities before they become threats. Now to identify and isolate threats before they can wreak widespread damage.
ITSM
Traditional, legacy cybersecurity measures are no longer adequate, if they ever were. Such measures tend to be reactive and remedial, in parallel with the “break/fix” approach to early attempts at ITSM. Today, both effective ITSM security and effective cybersecurity require solutions and processes that are proactive, prescriptive, and preventive, as well as able to respond to problems after they occur.
All of this means that cybersecurity can no longer be viewed as something separate from ITSM or IT management in general. Every IT activity at your business now requires a security component.
IT Discovery
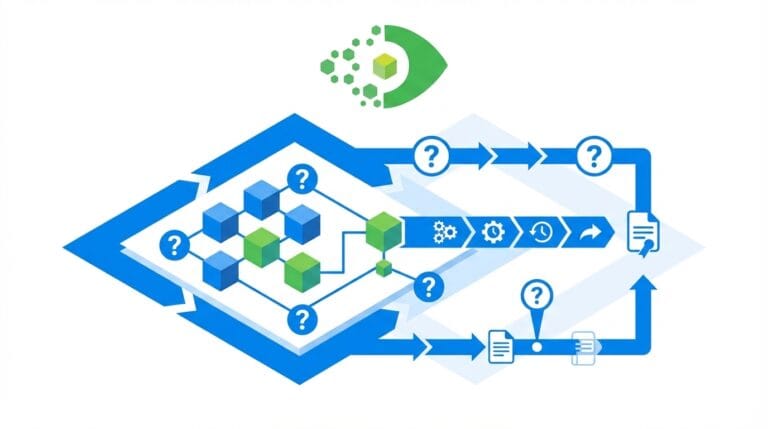
IT Discovery cannot simply catalog devices. Also, it must also include information about the relationships that link devices to each other, your services, and your users. IT Discovery and monitoring must also be constantly vigilant for unknown devices and unauthorized connection attempts.
ITAM
Similarly, your IT Asset Management (ITAM) efforts must embrace cybersecurity as well. The information you collect and store about your IT assets must be accurate, comprehensive, and timely, so your security patches, software updates, and other preventive measures are implemented consistently.
Every business and IT service you provide must be crafted, delivered, and managed with security as a primary concern.
Information Security and Cybersecurity
Operationally, all of this is a great incentive to bring IT and cybersecurity operations closer together, as discussed in a recent webinar co-hosted by Virima and follow-up. Technologically, you need IT discovery, ITAM, and ITSM solutions that capture and deliver the information you need to maximize the effectiveness of security efforts across your entire IT estate.
In reality, your business can never be too secure, and can always be made more so. With the right perspectives, processes, and technologies, however, you can make and keep your business secure enough to survive and thrive, no matter how sophisticated or numerous cyber threats become.
Virima: Your Partner for Better Convergence of Cybersecurity Response Plan
Virima’s solutions for IT Asset Discovery, IT Asset Management (ITAM), and IT Service Management (ITSM) are all designed to help improve the management and security of your entire IT estate. In addition, they’re built to be easy to use and configure, and to produce useful, actionable reports about your IT environment, for IT managers and business decision-makers.
We help you and your service management team work more closely and effectively with your cybersecurity counterparts, to maximize availability, resilience, and resistance to threats to your IT estate.
Virima features can automatically discover and map your critical IT resources and the interconnections that link them to one another, your applications and services, and your users.
Virima is here to help. To get started, contact us today to schedule a demo and explore the possibilities!