ITAM for risk management
The digital economy is a tough place to be in if you do not understand the level of security your IT assets need. It is not enough to know when a computer or server goes down anymore. You need to understand which vulnerabilities are present in your company’s hardware and software, what can be done about them, and how much damage they could potentially cause if exploited.
That’s why risk management has evolved as organizations have become more reliant on their IT infrastructure—and must now focus on physical assets and data. For this reason, an IT asset management (ITAM) tool should be integral to your risk management strategy.
Risk management refers to identifying, assessing, and mitigating potential threats and opportunities that could impact your organization. It helps companies plan for potential challenges by identifying possible scenarios, testing their effectiveness, and preparing appropriate responses.
This article will discuss the importance of risk management for IT security and why ITAM software should be a critical part of your risk management strategy.
Risks of not managing your IT assets
Risk management has evolved to include more than just managing physical assets. It now also includes protecting the access and integrity of your data to ensure that it stays safe.
While physical assets act as the gateway into your infrastructure, the data is your most valuable asset. Imagine a scenario in which you do not manage your IT assets. What would be the consequences of this?
You could expose your business to huge costs or data breaches due to lost or stolen devices, outdated assets, and poor backup policies. This liability means that your company will not only lose money but will also be unable to address its client’s needs as quickly or effectively as it otherwise could have. As businesses run on reputation—a tarnished one could mean lost customers so, you need to ensure that your assets are well managed.
Additionally, your IT costs can increase when you do not have fail-safes in place. You could be paying more than necessary because they are not used more efficiently. A lack of management also means it is harder to track down which devices are being used by whom—and whether or not they have been paid for.
ITAM provides the asset visibility that risk management depends on, and embedding asset data into a formal IT operational risk management framework ensures that risk assessments are grounded in accurate, discovery-backed inventory rather than assumptions about what exists in the environment.
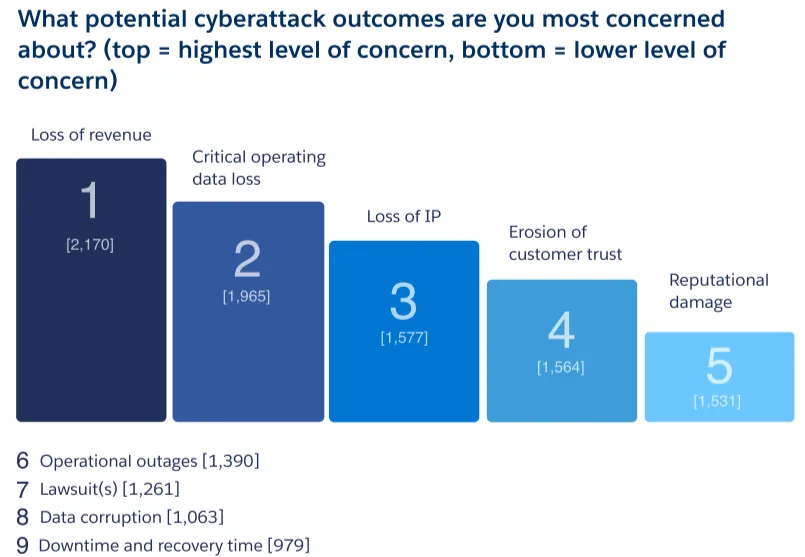
Let’s have a look at Salesforce report
A Salesforce report found that loss of revenue, loss of customer trust, downtime, and recovery time due to cyberattacks were some of the top priority concerns. When you consider that the average cost of a data breach ranges between $3.96 million and $4.24 million, increased downtime and loss of productivity can be incredibly costly. Not managing your IT assets is also an open invitation to cybercriminals who could take advantage of your company’s lack of security measures.
IT asset management should be part of an ongoing program that monitors changes in your IT environment on an ongoing basis. You can use this as part of a proactive risk mitigation strategy to identify potential problems before they affect your organization’s operations or information security posture.
In addition, this process can help you identify opportunities to be more efficient in your operations, such as by consolidating IT resources or retiring old, outdated technology. It is crucial for organizations with branches in multiple locations with different capabilities, such as a central data center or warehouse.
Types of risks that can be managed using ITAM
Technology risk can take many shapes and impact your organization differently, whether a cyberattack, data breach, or natural disaster.
Understanding the significant types of technology risk can help you determine your company’s risk exposure and develop effective mitigation strategies. Some of them include the following:
- Security risk: This type of risk refers to possible unauthorized access to confidential information stored on an IT system leading to its modification or destruction. Security risks often result from insufficient password protection policies or weak network security controls such as firewalls and intrusion detection systems (IDS). Examples include malware, unauthorized access, and data loss.
- Financial risk: This type of risk involves the economic liability of losing an IT asset or service. It also includes the possibility that costs will increase due to high-priced equipment failure or data loss. Financial risks often result from poor inventory management practices or inadequate disaster recovery plans. Examples include a lack of replacement assets and a loss in revenue.
- Operational risk: Operational risks are those that can affect your day-to-day operations and can have a direct impact on your revenue. A few examples include outages, service disruptions, and shadow IT devices.
- Legal risk: This type of risk refers to potential legal exposure caused by the loss or corruption of confidential data belonging to customers, clients, or partners. Legal risks often result from insufficient security measures or insufficient disaster recovery planning. Examples include compliance issues and expired agreements.
Based on these risk types, here are a few risks ITAM tools help you avoid:
1. Misuse and mismanagement of physical IT assets
ITAM solutions can prevent misuse or mismanagement as they help you monitor usage, ownership, and other aspects of the devices. It reduces risk by ensuring that only authorized users can access your organization’s sensitive and confidential data.
2. Compatibility of hardware with software products
ITAM tools assess the compatibility between software and hardware assets, ensuring that you do not invest in incompatible products.
By taking a proactive approach to ITAM, organizations can prevent wasted investments and piling up redundant assets in their inventory. These tools will thoroughly evaluate existing hardware and software to identify potential incompatibilities, allowing organizations to eliminate unnecessary costs associated with purchasing unsuitable products.
3. Inventory accuracy and visibility into IT assets
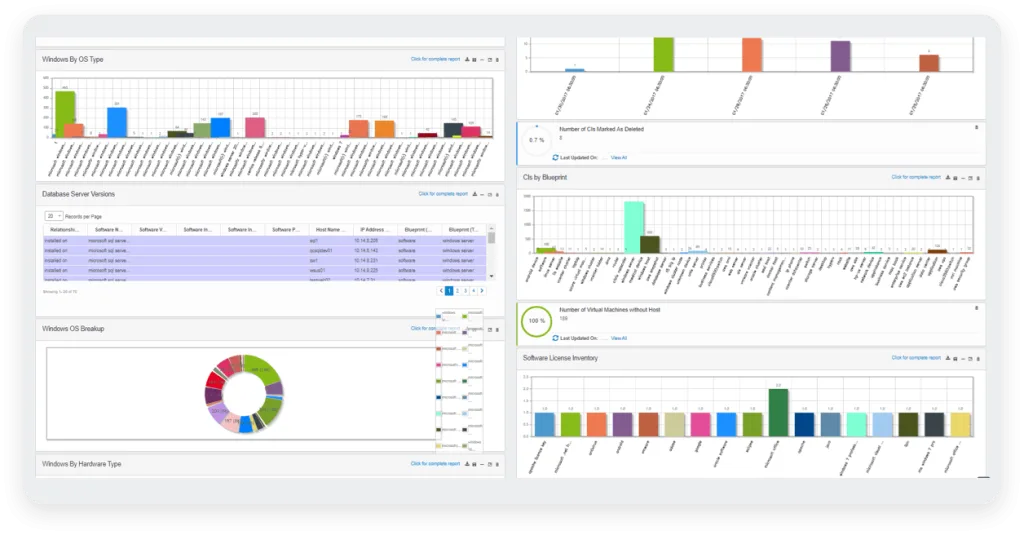
These tools allow organizations to gain insight into their network’s hardware, software, and other assets. They make asset management more manageable by providing an overview of the current state of their IT assets, enabling them to identify asset risks better.
Additionally, they provide detailed information such as asset serial numbers, purchase date, vendor, and usage data. With this information, organizations can track their hardware and software lifecycles (asset lifecycle management) while assessing their IT components’ performance.
4. Disposal of IT assets in accordance with legal regulations
These tools enable organizations to track assets’ retirement, disposal, and recycling. Companies can ensure that all retired assets are entirely wiped from the system or physically destroyed. It ensures that you cannot reuse data or software.
Plus, specific components such as RAM or graphics cards that may still have some value can be removed for reuse or stored for future use. Depending on local laws, organizations may also have the option to sell or donate devices if possible.
5. Lack of software compliance with regulatory requirements
ITAM tools provide the means to monitor software licenses and identify non-compliance before it becomes an issue. The tools offer user-friendly dashboards that allow organizations to keep track of their installations. This ensures they have sufficient licensed copies, and track usage rights such as the number of users or type of license purchased.
By monitoring software licenses and flagging non-compliance whenever it happens, organizations can ensure that they remain compliant with their licensing agreement while keeping costs under control.
6. Controlling expenditure on unnecessary assets
An IT asset management system allows you to track every device on your network, so it’s easy to determine which devices are being used by each employee and what they are being used for.
With this type of data at your fingertips, you’ll be able to analyze trends to make better decisions about where your technology budget should go next year. You could also determine how much money you should invest in upgrading specific systems or software packages within your company’s infrastructure.
7. Ensuring the organization is audit-ready at all times
ITAM tools are highly effective at ensuring organizations remain audit ready, as they provide a comprehensive monitoring system that helps organizations keep track of their assets and comply with industry standards.
The tool can automate regularly auditing the organization’s assets so that you can promptly address any changes or discrepancies. It ensures that all relevant information is always up-to-date and accurate, allowing organizations to respond quickly to any potential issues and prevent costly delays in the audit process.
8. Management of cloud assets and vendors
Using the right ITAM tool can help IT teams proactively monitor, inventory, and audit cloud applications to ensure the security of their data. For example, a good ITAM tool should enable visibility into assets such as where they are hosted, who has access to them, and which are active/inactive at any given time.
How to use ITAM to manage and reduce risks associated with IT assets
Now that you know what kind of risks you can expect within your infrastructure, here are a few ways ITAM can mitigate those risks:
1. Verification of IT assets before purchasing new assets
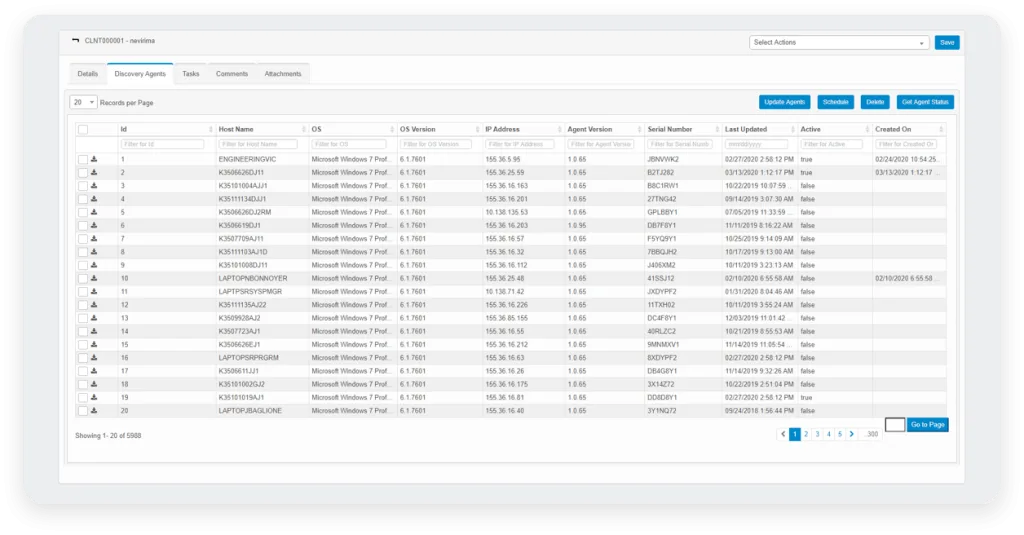
These management tools allow IT asset managers to evaluate the IT infrastructure they manage using automated technology. ITAM tools use advanced asset discovery technology, which continuously scans IT networks, to accurately detect all IT assets and gaps in the IT infrastructure.
By reducing the manual effort required to track IT assets and determining where gaps exist, IT asset managers can quickly verify the presence of IT assets and take corrective action on areas that need attention. It helps them make informed decisions about their investments, thus saving time and maximizing resources.
In addition, ITAM tools help automate the management process for IT asset administrators so they can focus more on driving business value through efficient IT operations.
For example, tools like Virima have agent-based and agentless flexibility to allow you to discover assets using varying methods. Plus, you also have the option to use the Windows Discovery Agent for network-connected devices in case there are additional security or credentialing concerns.
Plus, before any audits, you can look up the warranty status of your assets/licenses and ensure everything is up to date.
2. Strike a balance between user and company needs during procurement
During the asset procurement stage, ITAM tools enable asset managers to accurately balance the requirements of their company with those of the employees.
For example, if an employee advises that they need a specific type of IT asset. The manager can cross-check this data with existing company goals and objectives and decide whether or not its addition will provide true value. ITAM is, therefore, able to take into account both individual requests and the company’s need to ensure that all IT assets offer genuine benefits.
Here are a few things you can cross-check before making the decision:
- Available budget for the purchase
- Time frame needed for the procurement of this asset
- Budget alignment with current cash flow
- Individual/department needs for the specific asset
- Alignment with current business objectives
3. Deployment of assets and related updates only when needed
Through the use of ITAM tools, companies can automate processes such as:
- Asset auditing
- Categorizing and managing physical inventory
- Asset-tracking and tagging
- Reporting on current asset utilization
- Disposing of assets according to legal requirements
These tools provide insights into the status of IT assets and the current level of IT utilization within an organization. Using Virima, you can set status designations depending on how you tag assets in your organization. For example, you can set statuses like requested, ordered, development, production, and decommissioned, depending on the stage of the asset lifecycle.
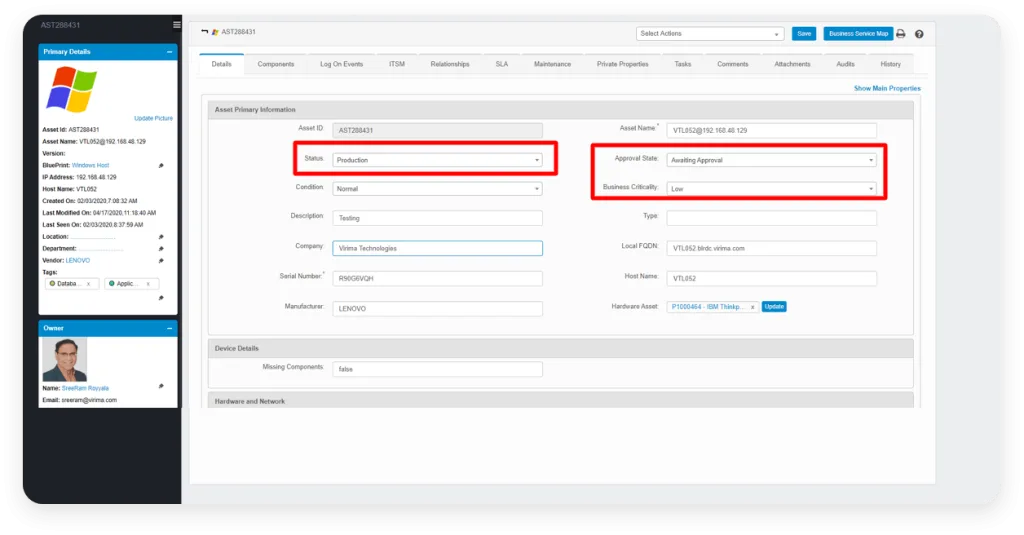
By monitoring these metrics regularly, asset managers can identify when new hardware or software upgrades are necessary and when it is better to avoid making changes during peak operational times. For example, if your asset is decommissioned, there is no point in deploying an update.
Also, ITAM reduces IT costs by improving asset utilization and mitigates risk for IT operations, allowing processes to run as reliably and efficiently as possible.
4. Spot opportunities for efficiency and growth using one tool
Additionally, you can use ITAM tools to automate specific processes, such as the auto-renewal of licenses or auto-updates for new versions of critical applications. It is vital in helping ensure compliance with the terms and conditions set by the software vendor.
These tools can also help reduce costs by giving visibility into the total cost of ownership (TCO) of entire IT infrastructures. Through TCO analysis, organizations can identify areas where they can save by consolidating overspending on unnecessary licenses or migrating from one platform to another with more cost-efficient options.
Additionally, you can track changes made and identify any anomalies quickly without disrupting productivity or workflow. 77% of CISOs consider automation the only way to keep up with newly deployed modern cloud-native application environments. So, by leveraging an ITAM tool in tandem with other security measures like encryption, and authentication protocols, organizations can ensure that their cloud-based data is safe and compliant with relevant regulations.
5. Improved end-user experience due to automated management
By automating the process of tracking, refreshing, and replacing assets, you can save time on manual audits. It allows you to shift your focus to more important tasks, such as preventing risks in their system.
In addition, with the ability to capture IT service desk tickets and requests from end users, asset managers are provided with real-time insights into what the users need and require for them to be productive. You can do this by integrating your service management tools with Virima and monitoring everything in one place. It also prevents the need to context switch between multiple applications, hastening the time to resolution.
Plus, users know that their equipment will always remain up-to-date, directly impacting their work performance positively. Overall, these tools help organizations make better use of their resources while avoiding costly errors or mismanagement due to outdated information or inaccurate records.
Manage IT risks using Virima’s ITAM tool
Even if you are not required to have an ITAM program, you can still gain from establishing one due to its convenient and cost-effective nature. You will be able to track changes that occur on your network systems and record when any changes are made. It will allow you to reduce the chances of unknowingly adding to an existing vulnerability.
Once your data is cataloged, it will be simple to detect any gaps or discrepancies in your environment. A great way to avoid being blindsided by a loss or failure is to view your hardware and software assets comprehensively. By deploying asset management software, you will lay the groundwork for your risk management process.
If you are looking for an IT asset management solution for risk monitoring, book a demo with Virima today.






