How Business Service Mapping improves ITSM processes
Let’s start with a simple question. What does the lack of business service mapping-driven IT visibility look like? It simply translates into a lack of clarity of intricate relationships within your IT environment. This poses numerous challenges. One of which is hindering the functioning of efficient IT service management processes.
As for the impact on specific ITSM processes, the struggle to identify critical dependencies can lead to delayed incident resolution and prolonged downtime. It also inhibits effective change management, making it harder to assess the impact of changes and implement them seamlessly. Furthermore, inadequate visibility into dependencies can leave organizations vulnerable to security breaches and hinder effective risk management.
Therefore, it is crucial for organizations to address this issue and strive for enhanced IT visibility through Business Service Mapping.
In this blog post, we’ll explore the importance of business service mapping for various ITSM processes within an organization. But before that, let’s understand what business service mapping is.
Understanding IT visibility through business service mapping
IT visibility refers to an organization’s ability to see and understand its IT infrastructure. This includes its hardware, software, and services and the relationships between all of these.
IT visibility also means having a clear picture of an organization’s IT infrastructure. So that it helps while
- responding to incidents,
- managing IT risks,
- resolving problems or
- making informed decisions regarding IT investments
A crucial component of IT visibility is business service mapping. Business service mapping allows organizations to map the relationships between their IT infrastructure and the business services they support. Such mapping would cover cloud-based, on-premise as well as hybrid services.
Also read: Why is a business service map critical for IT management?
However, the importance of business mapping lies in helping organizations to visualize how their IT infrastructure supports critical business services. It also identifies the components that make up each service and portrays the dependencies between them. Some service mapping solutions like ViVID service maps allow you to assign meaningful names to relationships. Coupled with such naming options, vibrant color coding of asset-to-asset connection makes understanding the relationship better.
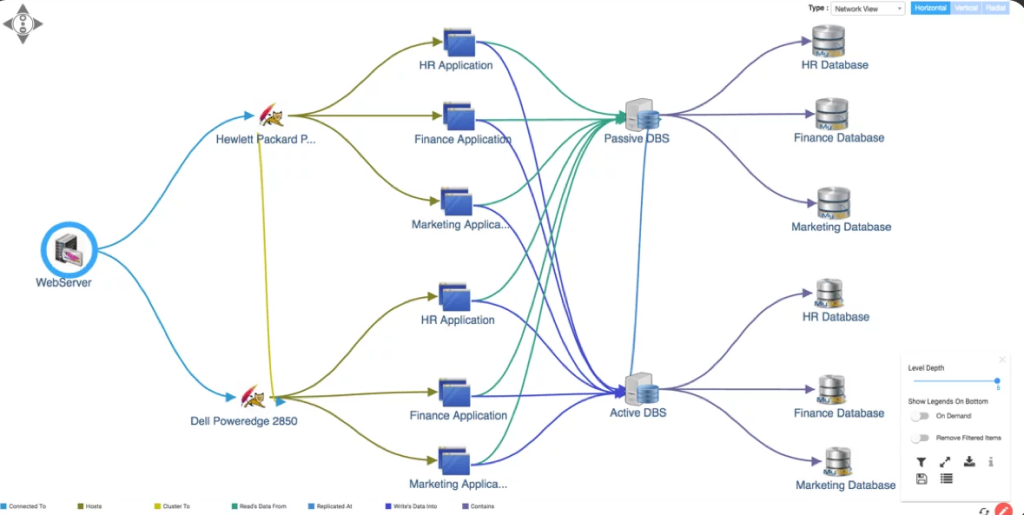
Image name: relationships between database and business services (HR, Finance Applications) in ViVID service maps through network view
At the granular level, business service mapping is the process of creating a visualization of the relationship between configuration items (CIs) and the services they form the backbone of. Along with that, it shows the relationship between the CIs and how they depend on one another.
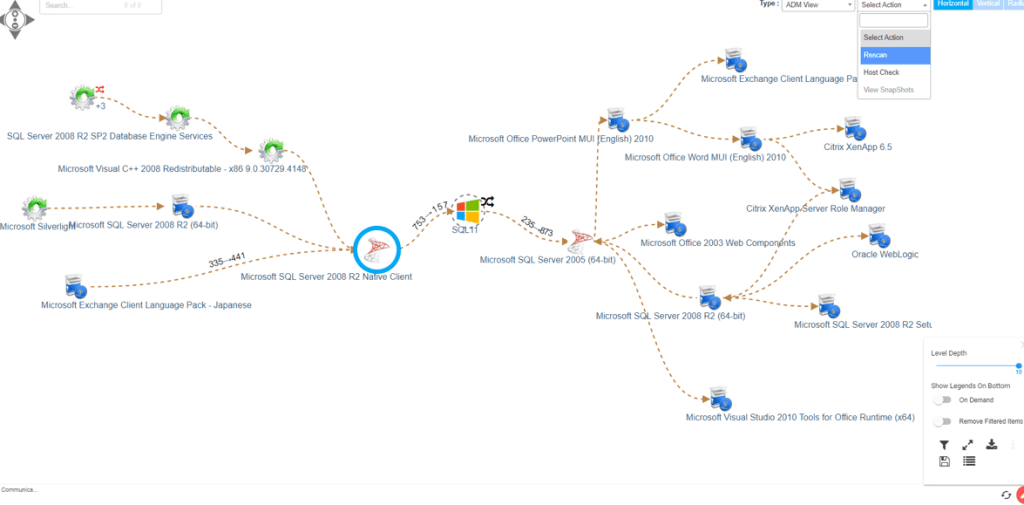
image name: Dependencies between CIs (servers) in Virima – ViVID Service Mapping
When you tie business service mapping capabilities with IT service management platforms, the IT visibility gained through it can help find the cause behind a reported service issue. It also shows the potential impact a service can have due to an issue reported to a CI.
The map itself will overlay the event or incident against a configuration item (CI) registered through the ITSM platform.
Importance of business service mapping for enhancing ITSM processes
Efficient incident management
Business service mapping ties business services like an order management service for an online retail giant with applications, systems, and the whole IT infrastructure. While on one level it shows a high-level view of dependencies and architecture, on the other, it identifies all the components (Configuration Items) involved in running a given service.
Proactive incident management
This 360-degree view helps in efficient incident resolution. Imagine a system monitoring tool alerting excessive RAM or CPU usage on a server. Now two situations can follow. In one, a responder can log the incident to route it to the right department to handle. In the other situation, the system automatically ties this initial alert to the right CI in CMDB. At the same time, the system creates an incident and assignment based on predetermined priorities, and it displays them on a service map like ViVID™.
Now, the person responding to the incident can rapidly assess how the RAM or CPU issue would impact the business service(s). This allows for proactive handling of the incident before any disruption is noticed.
Responding to incidents: Accelerating the MTTR
Despite such automated altering and preparation in incident management, things can quickly escalate and go wrong. It may be a failure of a critical asset that disrupted service of high demand resulting in a P1 situation. Due to the asset failure, multiple services might experience downtime.
The first thing to do in this scenario would be to get to the root cause. But that pops up a bunch of questions such as what’s the common link to all the reported service disruption? What change is possibly causing it? What went out of control?
Service maps such as ViVID™can answer not only what changed but also show what one service disruption has to do with the other disruptions. It’ll show how the CIs are related and support multiple services. For instance, the maps will show how a shared database server (a separate CI) can serve multiple services or applications.
When coupled with an ITSM platform like Jira Service Management, ServiceNow®, and Ivanti, the service maps would tie the open incidents to the underlying components of infrastructure. Along with that, all the planned changes or recently completed changes would be there on the dynamic visual maps. On top of this, you can compare the original service map with the current one to view changes made to its architecture.
Such IT visibility would enable you to quickly identify the root cause of failure. As a result, accelerates the MTTR.
Business service mapping for better change management
Evolving business needs call for change. The pressure for carrying out that change goes to IT and a rush happens. That rush converts into severe consequences for organizations. In the case of Knight Capital Group, a software update with an untested feature cost them $440 million as their automated trading system malfunctioned.
This was a decade ago. Since then organizations have leaned towards change management processes that are matured to avoid such dire errors. However, to keep up with the rapidly evolving IT landscape, changes should be applied fast.
The importance of business service mapping-led IT visibility lies in the fact that it meets both ends– ensuring smooth change devoid of severe consequences and speeding the process to keep up with the trend. It does so by showing the potentially impacted devices when a change is proposed for a certain CI.
It shows the change collisions and helps create the change agenda for the CAB (Change Approval Committee). Moreover, the service maps allow for easy identification and coordination with stakeholders. This makes it easy for stakeholders to get involved in the change approval and also plan service delivery according to the proposed downtime.
The business service mapping feature also provides additional IT visibility to change planners to view other changes that should be completed first or else could introduce additional risks.
Security and vulnerability management
When it comes to security and vulnerability management, business service mapping helps in prioritizing security risks and subsequent addresses. Once you get the vulnerability report, the dynamic maps make it easier to identify the CIs in the organization that match the report. Then it allows you to view the business services supported by the CI in question and determine how critical they are.
Based on the findings, IT teams understand the specific services that are potentially at risk, as well as which IT assets are dependencies or integral to the delivery of these services. Moreover, service maps like ViVID service mapping overlay the assets having NVD vulnerabilities in the dynamic maps in each view- infrastructure, network, etc.
Accordingly, this allows IT teams to allocate resources based on the criticality of the vulnerability as per the CVE (Common Vulnerability Exposure) in NVD. They also get to prioritize vulnerability remediation efforts based on the criticality of the business service that the CI in question supports.
For example, let’s say an organization detected a vulnerability on that server (a CI) that supports a critical business process such as payroll processing. So it could potentially impact the payroll processing service and, in turn, negatively affect the entire business. With business service mapping, the organization can quickly assess this risk and prioritize the appropriate measures to patch or remediate the vulnerability, ensuring a lower risk of unexpected downtime or potential data breaches.
IT visibility for disaster recovery planning with business service mapping
One of the most crucial steps in disaster recovery is to mark the most crucial applications, systems, business services, data, and other IT resources. Such identification works towards ensuring the continuity of the most crucial business services when a disaster takes place. For that, the disaster recovery plans include the steps necessary to recover and ensure business continuity.
In this regard, the IT visibility provided by business service mapping helps identify the most critical IT assets by creating an inventory of them. The dynamic visualization provides a detailed service catalog and shows the way they work together or are dependent.
So once you know the configuration of your network infrastructure and the location of each critical application, you’ll also see the communication pathway of the applications.
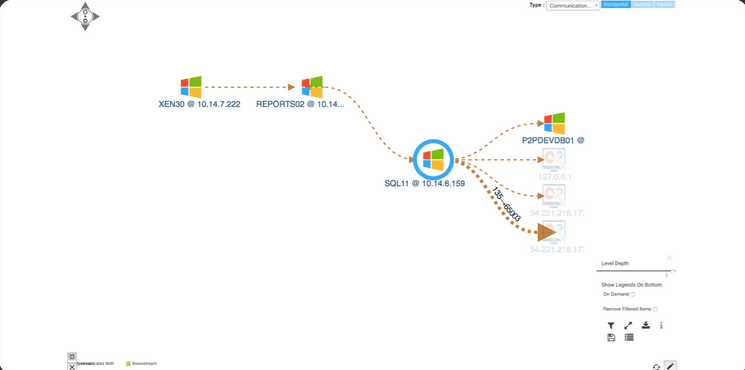
image name: communication view in Virima ViVID service maps
This will give you an idea of how failure due to a disaster or outage can have an impact on business services.
Also read: Service mapping and disaster recovery planning
Suppose a company has business service mapping integrated into its IT environment. So it identifies a critical server or application that is central to multiple business functions, such as order processing and inventory management. In that case, the mapping can provide critical insights into the dependencies and applications that rely on that server. Mapping out its dependencies reveals that the server serves as the backbone of the inventory system.
So when a disaster or outage occurs, your disaster recovery plan should mention the systems to be restored first to resume operations quickly. In the above case, a natural disaster or a severe cyber-attack can impact the data center where the server supports order processing.
Due to the understanding of the criticality of the service and a clear idea of dependencies, businesses can establish specific recovery procedures as per the disaster recovery plan. This can include backup strategies, alternate failover locations, and recovery timelines. It’ll ensure that employees or customers get the least impacted.
Enhance ITSM processes with ViVID business service mapping led IT visibility
The importance of business service mapping in a complex IT landscape is observed in the incident, change, security, and vulnerability management. In these processes, the dynamic visualization of relationships and dependencies between IT assets, systems, and business services is what benefits them.
The same business service mapping led IT visibility is essential for creating disaster recovery plans. Here it identifies the most crucial components of IT infrastructure that should be restored first. So that operations can resume quickly and ensure the least impact on customers and employees.
For all of the above use cases, one of the market-leading business service mapping solutions is ViVID service mapping from Virima. What makes it special is its ability to work in integration with major CMDB and ITSM platforms such as ServiceNow, Ivanti, and Cherwell. Moreover, its automatic visualization of complex CMDB relationships phases out non-CMDB assets relationships by pointing out any external system having suspicious communications.
At the same time, it provides holistic network and infrastructure views to be used in all the IT processes listed above. Request a demo to integrate business service mapping-led IT visibility into your IT environment and streamline IT processes.






