What Is a Configuration Item (CI)? Definition, Examples & CMDB Guide
On March 1, 2024, Microsoft went dark. It was a massive outage. Outlook, Teams, Exchange, and even Azure all went down.
Tens of thousands of users were locked out. Businesses stalled. Productivity froze mid-click.
One glitch sent a ripple across the entire Microsoft ecosystem.
And here’s the thing: figuring out what caused the outage put the ‘trust’ customers had placed in Microsoft under a microscope. Eventually, it was all sorted. But the initial blame went to CrowdStrike, its cybersecurity vendor.
This is what happens when IT systems stretch across hundreds of servers, apps, and networks. One weak link, and the whole chain snaps.
Downtime isn’t just annoying. It’s expensive. Some studies put it at $9,000 per minute. That’s a bleeding edge nobody wants to be on.
The problem? Most organizations can’t actually see all their moving parts.
Servers are here. Databases there. Software licenses are floating somewhere in the middle. All siloed, all critical, none fully mapped.
This is where the CMDB configuration item comes in.
Track every component. See the dependencies. Know the blast radius before something fails.
In this guide, we’ll break down what a configuration item is, the different types, and best practices to manage them. Your team can spend less time firefighting and more time running IT the way it should.
What is a configuration item in ITIL?
A configuration item (CI) is any component or resource in an organization’s IT environment that needs to be tracked and managed to deliver services. In ITIL configuration management, CIs are tracked for their existence, relationships, dependencies, and impact on services.
CIs can include:
- Physical assets like servers, network devices, and laptops
- Digital assets like applications, virtual machines, and cloud services
- Documentation such as policies, process diagrams, and service-level agreements
- People in roles such as service owners, administrators, or specialists
- Facilities like data centers, network rooms, or other service-critical locations
A CMDB stores detailed records about each configuration item and its connections. This helps IT teams:
- See how services depend on each other
- Assess the impact of changes before they happen
- Cut downtime by improving incident and problem resolution
Keeping CI records accurate within ITIL configuration management practices helps organizations make better decisions, reduce service disruptions, and align IT operations with business goals.
Types of configuration items in CMDB
In a configuration management database, a configuration item can be almost any component needed to deliver and maintain IT services. To simplify management, CIs are grouped into clear categories.
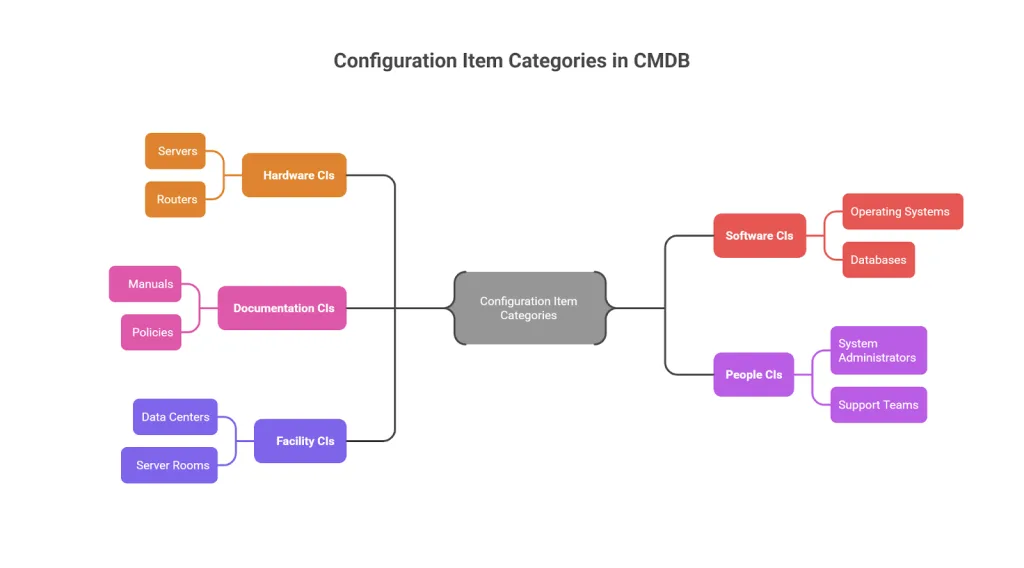
Configuration item categories in CMDB
Hardware CIs
Hardware Configuration Items include all physical devices in your IT environment: servers, laptops, desktops, routers, storage systems, and network switches. These are the tangible components that IT infrastructure runs on.
Software CIs
Software Configuration Items cover applications, operating systems, databases, middleware, and virtual machines, including those in cloud environments. Tracking software CIs helps teams understand what’s deployed, where it runs, and how it interacts with other components.
Documentation CIs
Documentation CIs include manuals, support guides, configuration diagrams, policies, and process documents. While intangible, they’re critical for troubleshooting, compliance, audits, and keeping operations consistent.
People CIs
People CIs capture the roles, responsibilities, and relationships of individuals managing or using IT services. System administrators, service owners, and support teams all fall into this category. Tracking people as CIs keeps accountability and operational clarity in check.
Facility CIs
Facility CIs include physical locations that support IT operations: data centers, server rooms, or disaster recovery sites. These are tracked because they provide the environment where IT services run.
Categorizing Configuration Items into hardware, software, documentation, people, and facilities gives organizations a structured view of their IT environment. That structure makes it easier to manage dependencies, relationships, and service impacts.
What are CI attributes, and what data should you track?
Every configuration item in your CMDB should carry a core set of attributes that describe what it is, where it sits, and how it connects to other components. Common CI attributes include the CI name, unique identifier, type/category, owner, location, version, status (active, retired, in test), and relationships to other CIs.
For hardware CIs, you’d also track serial number, manufacturer, model, warranty status, and IP address. Software CIs need version number, license type, vendor, and install location. The goal is to capture enough detail that any IT team member can understand the CI’s role in service delivery without digging through separate systems.
Start with the attributes that matter most for incident response and change management. You can expand the data model later as your CMDB matures.
Configuration item vs. IT asset: What’s the difference?
It’s common to confuse Configuration Items with IT assets. They serve different purposes in IT management.
An IT asset is any hardware, software, or resource with financial value for the organization. Think laptops, servers, software licenses, or cloud subscriptions. IT Asset Management focuses on costs, contracts, and lifecycle management.
A configuration item is about service delivery and operations. A CI could be an IT asset, or it could be something with no direct financial value, like documentation, a database connection, or a virtual service dependency that affects IT services.
| Aspect | Configuration item (CI) | IT asset |
| Purpose | Service delivery and operational impact | Financial value and lifecycle management |
| Scope | Includes assets and non-asset items | Focuses only on owned/purchased items |
| Relationships | Tracks dependencies and service impact | Tracks cost, contracts, and ownership |
| Examples | Servers, firewalls, configs, documentation | Laptops, software licenses, cloud spend |
Some items qualify as both assets and CIs. CIs focus on keeping services reliable. Assets focus on managing costs and ownership. Virima brings both views together by combining ITAM with CMDB and service mapping, so teams see financial and operational context in one place.
Why Configuration Items matter in ITSM processes?
Configuration Items are the building blocks of IT service management (ITSM).
From servers and cloud instances to business applications and supporting documentation, CIs give IT teams full visibility into the infrastructure powering business services.
CIs also form the operational spine of incident resolution, change impact analysis, problem prevention, and compliance. When managed through a CMDB, they help IT organizations turn raw data into insights that directly affect business continuity and cost control.
What happens when configuration item data in your CMDB is inaccurate?
Inaccurate CI data leads to blind spots during incidents, failed changes, and compliance gaps. If your CMDB shows a server running one application when it actually supports five, a routine patch can trigger an outage nobody predicted.
Stale CI records also undermine root-cause analysis. Teams waste time chasing the wrong dependencies and miss the actual failure point. Over time, trust in the CMDB erodes, and teams fall back on tribal knowledge and spreadsheets, which only makes the problem worse.
Automated IT discovery solves this by running recurring scheduled scans that keep CI records current. Instead of relying on manual updates, tools like Virima continuously reconcile what’s actually running against what’s recorded in the CMDB.
Reducing downtime during outages: incident management
HealthSure Hospitals relies on Electronic Health Record (EHR) systems to provide patient information. One morning, the EHR system slowed to a crawl across multiple departments.
The IT team used the CMDB to identify all dependent CIs: EHR application servers, database clusters, and network gateways. They quickly found that the database cluster supporting multiple clinical systems was near capacity.
Using Virima, the team identified 12 servers supporting the application, far more than the four the vendor had documented. Resources were reallocated quickly, and the CMDB was updated with incident and corrective actions.
By maintaining accurate CI relationships, HealthSure resolved the outage in under 45 minutes.
Virima case highlight:
- Automated discovery of over 7,000 server configurations and 2,000 applications in this deployment
- Mapping of 150+ enterprise services so teams always know the full scope of dependencies
Configuration item (CI) lifecycle in ITIL 4
Managing the configuration item lifecycle ensures accurate records, better control, and efficient service delivery across ITSM processes like change enablement, incident response, and problem management.
Planning and design
This stage starts with identifying the business need for a new CI. IT and business stakeholders decide what type of configuration item is needed (server, application, database, etc.) and define its specifications, expected relationships, and compliance requirements.
Setting clear goals upfront prevents unnecessary complexity and ensures each CI adds real value to IT services.
Acquisition and procurement
Once requirements are defined, the CI is purchased, licensed, or developed according to the agreed design. This may involve vendor negotiations, cost approvals, and alignment with security or architectural standards.
Identification and registration
Every configuration item must be uniquely identified before entering the live environment. This includes:
- Assigning a unique CI ID
- Categorizing the CI type (hardware, software, documentation, people, facilities)
- Documenting attributes such as version, owner, location, and relationships in the CMDB
This ensures traceability and links the CI to incidents, changes, or service requests later in its lifecycle.
Testing and quality assurance
Before deployment, the CI is placed in a test or staging environment. IT teams validate whether it meets performance, security, and compliance requirements. This step prevents flawed configurations from reaching production and reduces the risk of service disruptions.
Deployment to production
The CI then moves into the production environment following change management approvals. Deployment includes documenting the go-live date, dependencies, and rollback plans in case issues arise after release.
Early life support (ELS)
During the initial post-deployment phase, the CI gets enhanced monitoring and support. This “hypercare” period helps IT teams quickly address unexpected issues and stabilize performance before steady-state operations begin.
Production and operational management
The CI now operates as part of the organization’s live IT services. At this stage, IT teams handle:
- Monitoring performance and health metrics
- Applying patches and updates to keep it secure and compliant
- Recording incidents and changes linked to the CI for accurate impact analysis
Automation tools help maintain accuracy here by detecting changes through recurring scheduled scans.
Continuous review and optimization
Throughout its lifecycle, the configuration item undergoes periodic audits and reconciliations to ensure data accuracy and regulatory compliance. Outdated relationships or unauthorized changes are corrected to maintain CMDB reliability.
Retirement and disposal
When the CI becomes obsolete or is replaced, it moves into retirement. This involves:
- Safely removing sensitive data
- Redeploying or canceling software licenses
- Recycling or securely disposing of hardware
- Updating the CMDB to reflect the CI’s removal and prevent “ghost” dependencies
Proper retirement ensures cost savings, compliance with data privacy regulations NIST Privacy Framework or GDPR official resource), and a cleaner IT environment.
CMDB relationship mapping for Configuration Items
No configuration item exists in isolation. Servers connect to applications that rely on databases, which may run across multiple cloud environments. This is where service asset and configuration management plays a critical role in giving you full visibility. A single failure in one component can ripple across the entire service chain, causing outages, disrupting customers, and increasing risk.
Under ITIL configuration management, mapping relationships between CIs in your CMDB matters because it strengthens risk management, supports software asset management tools, and aligns with broader enterprise software asset management goals.
- Service impact analysis. When a CI fails, dependency mapping shows which applications, users, or business services are affected so IT leaders can prioritize what to fix first.
- Root-cause analysis. Tracing issues back to the exact failing component reduces mean time to resolution MTTR instead of just firefighting symptoms.
- Prevention of cascading failures. Understanding how CIs connect lets IT teams plan changes or updates without accidentally breaking downstream services.
- Faster incident response. Visual maps help even non-technical stakeholders grasp the scope of an outage or planned change quickly.
Traditional CMDBs display data in tables and lists. Virima’s Virima Visual Impact Display (ViVID™) goes further by overlaying ITSM incidents, change records, event management alerts, and NIST NVD vulnerabilities onto dynamic service maps. The NVD integration is included at no additional charge, so vulnerability context sits alongside your CI maps without a separate license. IT leaders can:
- See relationships between servers, applications, networks, and cloud services updated through recurring discovery scans
- Visualize the potential impact of proposed changes before approving them
- Pinpoint critical paths during outages to speed up recovery
With ViVID™, you’re not looking at a static database. You’re getting a heads-up display of your entire IT ecosystem that supports faster, better-informed decisions.
Best practices for managing Configuration Items
Managing Configuration Items well keeps your CMDB clean, accurate, and useful. A few principles that make the biggest difference:
- Decide what to track. Focus on critical systems and services, not every minor component.
- Keep CI data consistent. Standardize fields like name, type, owner, and relationships for clarity.
- Follow a CI lifecycle. Add new CIs, update details after changes, and safely retire unused ones.
- Automate discovery. Use tools to track CIs and dependencies through recurring scans instead of manual spreadsheets.
- Map relationships. Visualize dependencies for better impact analysis and faster troubleshooting.
- Assign ownership. Make teams or individuals accountable for keeping CI data accurate.
- Audit regularly. Review data to maintain compliance and catch drift before it causes problems. Virima’s SOC 2 Type II certified platform supports audit readiness out of the box.
- Integrate with ITSM. Feed accurate CI data into incident, problem, and change management workflows.
How to manage Configuration Items with Virima
Here’s how Virima makes managing Configuration Items straightforward. All your CIs are organized and tracked through the CMDB with automated discovery and integrations.
The first step is getting your CIs into the system:
- Run Virima Discovery scans across your network (agentless, using hundreds of out-of-the-box, extendable probes and sensors)
- Deploy lightweight Discovery Agents for Windows, macOS, and Linux devices
- Integrate with cloud platforms like AWS or Azure
- Import data using CSV templates
Once your CIs are in place, Virima’s service mapping automatically connects the dots, showing how assets, applications, and services relate to each other. ViVID™ then overlays incidents, changes, and vulnerability data onto those maps. You can also add any missing links manually to keep the big picture clear.
If you’re already running ServiceNow, Virima syncs CI and configuration management data directly into your ServiceNow CMDB, so you get enriched discovery data without replacing your existing ITSM platform.
Inside the CMDB, you’ll find all the details about your Configuration Items along with visual maps that make change planning, impact analysis, and troubleshooting far easier to get right.
Book a demo today and see how Virima keeps your Configuration Items organized, mapped, and ready for action.
FAQs
Q1: What is the role of a configuration item in ITIL configuration management?
A configuration item is any component in your IT environment, whether hardware, software, documentation, people, or facilities, that must be tracked to deliver IT services reliably. In ITIL configuration management, CIs maintain a clear view of dependencies, which enables informed decisions for incident resolution, change management, and service continuity. Virima’s ITSM platform holds PinkVERIFY ITIL 4 certification for Service Asset and Configuration Management (SACM), so CI tracking aligns with verified ITIL practices out of the box.
Q2: How can an accurate CMDB improve ITIL configuration management processes?
A well-maintained CMDB stores detailed CI records and their relationships. This visibility leads to faster incident response, accurate impact analysis for changes, and fewer service disruptions. It helps IT teams align operations with ITIL best practices.
Q3: Which types of Configuration Items should be prioritized for tracking?
Start with CIs that directly impact service delivery: key servers, core applications, databases, network devices, business-critical documentation, and relevant personnel roles. Tracking these first ensures operational continuity and supports compliance.
Q4: How do Configuration Items support change management and incident resolution?
CIs make dependencies visible. Before making a change, teams can analyze affected CIs to prevent disruptions. During incidents, CI relationships help identify root causes quickly, which reduces downtime and improves overall service reliability.
Q5: What tools can help maintain up-to-date configuration item records?
Tools like Virima offer automated discovery with hundreds of out-of-the-box, extendable probes and sensors, recurring scheduled scans that keep CI data current, and machine-learning-driven relationship mapping. ViVID™ service maps then present near-real-time views of dependencies, infrastructure, and service relationships for smarter ITIL-driven decisions.






