Incident communication: A complete guide with best practices
Incidents are a normal part of business, especially for companies that rely heavily on technology and data. When an incident hits, it can disrupt your business processes, slow down product and IT service delivery, and even threaten the security of your data.
In these moments, a strong incident communication plan is critical to control the narrative, maintain customer trust, and reduce lasting damage.
For example, picture a global e-commerce company during its biggest annual sale. A major outage stopped customers from completing purchases, locked sellers out of their dashboards, and left the company silent for hours. Frustrated customers took to social media, and the problem quickly went viral.
News outlets soon picked up the story, criticizing the company’s poor communication. Even after systems were restored, the damage to the company’s reputation lasted. Further, trust eroded, stock prices dropped, and competitors gained an advantage.
The immediate effects of incidents show up as operational problems, but the long-term damage hits your reputation with customers, shareholders, and regulators. According to IBM’s Cost of a Data Breach Report 2024, the global average cost of a data breach reached $4.88 million.
This number grew 10% from last year and is the highest ever recorded. This clearly shows why strong incident management and incident communication matter. They help reduce both financial losses and harm to your brand.
Since communication is so important during incidents, this guide focuses on managing it well. You’ll learn how to handle communication from the moment you detect a problem to notifying stakeholders and crafting clear messages.
Key takeaways
- Incident communication is critical for keeping teams aligned and customers informed during service disruptions.
- Having a plan reduces confusion, protects your brand, and ensures faster incident resolution.
- Key components include: Clear roles, predefined channels, message templates, and audience segmentation.
- Real-time updates build trust and reduce pressure on support team members.
- Post-incident communication documents lessons learned and shows accountability.
- Virima enhances incident communication strategy with stakeholder mapping, visualized dependencies, and automated updates.
What does incident communication mean
Incident communication is the process of sharing important information about unexpected service problems with the right people. This includes both your team and outside contacts. According to ITIL, an incident is defined as an unplanned interruption to a service or a reduction in the quality of a service.
You need incident communication tools to keep things running smoothly in IT service management. It helps you share updates quickly and clearly from the moment you spot the problem until it’s fully fixed and reviewed.
A good incident response communication plan sets clear rules about who alerts whom and when. It also guides how to give real-time updates and keep customers and stakeholders informed. Whether it’s a system outage, slow performance, or a security issue, clear communication cuts confusion, sets the right expectations, and speeds up your team’s response.
Whether it’s a system outage, slow performance, or a security issue, clear communication cuts confusion, sets the right expectations, and speeds up your team’s response.
This raises an important question:
What is major incident communication?
A major incident is a high-severity outage or crisis that causes serious disruption to critical business services, such as a system-wide outage, security breach, or large-scale service failure. Because the impact is widespread, communication during these moments must be handled with extra care.
Major incident communication is the process of delivering rapid, transparent, and accurate updates to a broad audience—including internal teams, executives, customers, and external stakeholders.
Unlike regular incident updates, major incident communication requires frequent, clear, and coordinated messaging to reduce confusion, maintain trust, and demonstrate control during a crisis.
By focusing on structured communication, organizations can minimize damage to their reputation, meet service obligations, and restore normal operations faster.
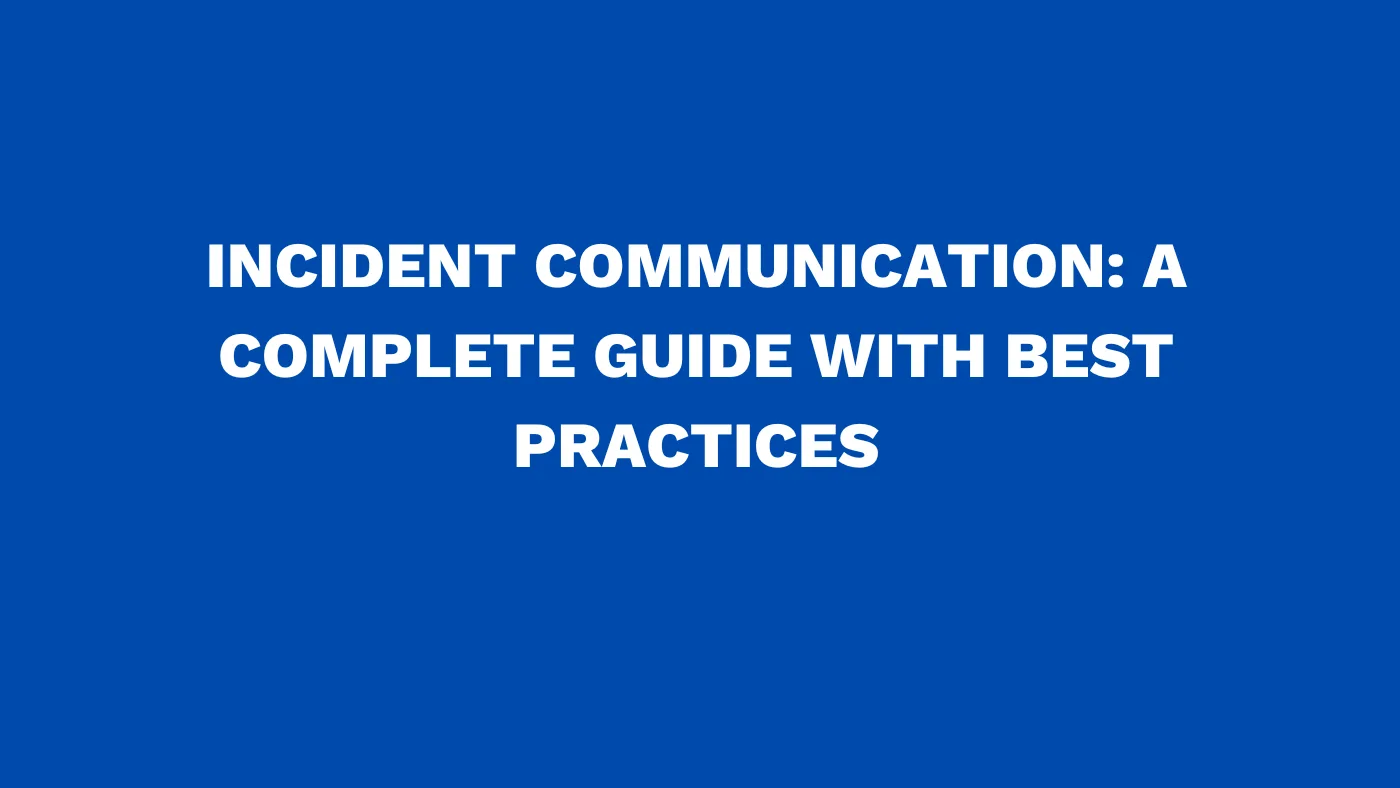
What you see in major incident communication
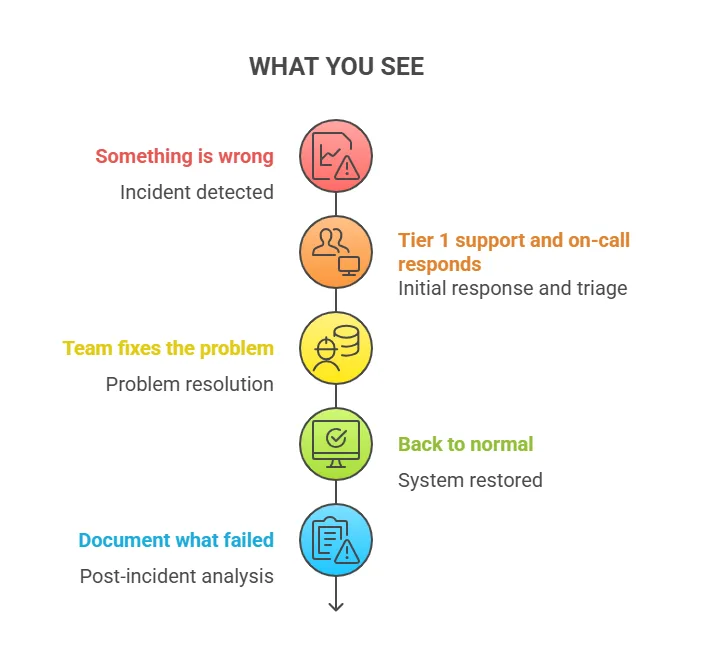
What your customer sees in major incident communication
Here are the key components of a critical incident communication plan:
- First, you need to clearly identify which channels you’ll use and how often you will send updates. Next, make sure everyone involved knows their roles and responsibilities.
- You should also prepare text message templates ahead of time. These templates keep your communication fast and consistent.
- Plus, integrating your communication with incident management tools lets you send automated status alerts without delay.
- After an incident, it’s important to share a detailed postmortem communication or retrospective. This review helps document what happened, what you learned, and how to prevent future problems.
When you follow these incident communication best practices, you strengthen your organization’s ability to bounce back. You also meet your service agreements and protect your brand’s reputation, even during tough disruptions.
Why is major incident communication as important as incident management
You need to be careful and clear when communicating with stakeholders during a major incident. This is because you control the story and how people understand what happened.
Without a clear major incident communication plan, customers will form their own ideas about the incident. They may base these ideas on incomplete facts or personal opinions. This can further create confusion and even harm your reputation.
Studies have shown that the perception of how you manage a major incident is often more meaningful to stakeholders than the technical details of the incident itself. In other words, strong major incident communication helps protect trust, even when the technical fix takes time.
That’s why it’s important to communicate with stakeholders early and often. This way, you build trust and also keep everyone on the same page.
Major incident communication: Step-by-step guide & best practices
Part I: How preparation improves major incident communication outcomes
Without a clear plan, even small problems can turn into big headaches for your customers and your team. That’s why preparation matters. When you know what to say, when to say it, and how to share it, you control how incidents unfold.
First, define what qualifies as an incident
Before you communicate about incidents, you need to agree on what counts as one. This means setting clear rules about how serious an incident is. Many teams often use a severity scale, from minor bugs to full-service outages.
Clearly define at what point an incident is considered “major” (for example, a Severity 1 full-system outage). When that threshold is met, your major incident communication protocol should kick in—escalating update frequency, expanding audience reach, and involving executives to ensure visibility at the highest level.
Link these severity levels to real measurements like how fast you respond, how long services are down, or how much the incident affects key business functions. For example, a Severity 1 incident could mean the whole system is down. A Severity 3 might be a small user glitch. Clear definitions remove confusion, especially when things get stressful.
Also, remember that IT security breaches and data loss always need immediate external communication, no matter the severity. This also keeps you accountable and follows security rules.
Select communication channels before major incidents occur
A solid incident communication plan picks channels and messages ahead of time. This removes guesswork and helps you respond fast and clearly when it matters most.
Here are important channels to consider:
- Status pages: These act as a real-time hub where customers, partners, and teams can check service status anytime. Subsequently, this reduces support calls and builds trust through openness.
- Email notifications: Email works well for sending structured updates. Use it to resolve incidents, share progress, and confirm fixes. Also, letting users subscribe keeps them informed and involved.
- Workplace chat tools: Internal chat tools help your teams work together quickly. During an incident, they cut delays and confusion by allowing real-time updates across departments.
- Social media updates: While not the main way to communicate, social channels help spread general news to a broad audience. They also reach users who might miss your official alerts.
- SMS alerts: For urgent issues, SMS grabs immediate attention. But be careful—too many texts can annoy users and cause them to opt out.
No single channel works for everything. Instead, layer your communication. Post updates on your status page, send email alerts, and keep internal chats in sync. This way, everyone—customers and employees—gets the right info through their favorite channels.
Part II: Ensure the right message reaches the right audience
Clear and timely communication is essential during any IT incident. It helps reduce confusion and improve response times. When people know what’s happening, they stay calm and trust the process. With the right strategy, you can make sure the right people get the right message at the right time.
As soon as an incident happens, communication should begin. Start with internal teams and then move to external audiences. To keep things simple, think of your audience as five main groups.
1. Core response team
This group spots the problem and takes action first. Monitoring tools usually alert them right away. Moreover, they work together to figure out what’s going wrong.
Quick and clear updates help them fix issues faster. Plus, real-time messages keep everyone in sync.
2. Front-line support
Support agents are your bridge to customers. They need accurate updates so they can answer questions clearly. If you don’t keep them informed, messages can get mixed up.
That can also frustrate your users. So, keep your support team in the loop from the start.
3. Managers and executives
Leaders must understand the size of the issue and how it affects the business. Give them clear updates so they can act fast and make smart choices. They also need to talk with other departments and outside partners.
Altogether, well-timed messages help them stay in control.
4. Internal employees
Don’t forget your internal teams. They need to know if their work will be affected. Further clear updates help reduce confusion and limit the number of support tickets. That way, your IT team can stay focused on fixing the issue.
5. External customers
If customers are affected, tell them what’s going on. Plus, let them know what steps you’re taking and when they’ll hear from you again. Even if there’s no fix yet, regular updates—every 30 to 60 minutes—show that you care. It also builds trust and keeps people informed.
Use templates to simplify the incident communication process
In the middle of an incident, finding the right words can be hard. That’s why templates are so helpful. They save time and make sure your messages stay clear and consistent. You can tweak them based on the issue at hand.
Here are a few examples:
- Investigating a Potential Outage
Subject: Investigating network performance issues
Message: We’re looking into reports of a possible disruption. We’ll share more details as soon as we know more. - Full Outage
Subject: Service interruption detected
Message: A full outage is affecting [affected systems]. We’re working to fix it. The next update will be shared by [time]. - Partial Outage
Subject: Degraded performance detected
Message: Some users may notice slower performance on [affected services]. We’re investigating and will provide updates shortly. - Scheduled Maintenance
Subject: Scheduled maintenance for [service name]
Message: Maintenance is planned on [date] from [start time] to [end time]. You may notice [expected impact]. Thanks for your patience.
Part III: Manage the major incident communication plan like a pro
Most major incidents follow the same steps: first response, regular updates, and a clear resolution. When you follow this structure, it not only keeps everyone informed but also improves how people view your team’s efforts.
Start major incident communication with internal alignment
Before sharing any news with users or stakeholders, get your internal team on the same page. Further, use one communication platform to help your team work faster. This also allows everyone to receive alerts, check the problem, and take action without delay.
When your internal process runs smoothly, it becomes easier to manage external updates.
In a major incident, the first update matters most
The first message you send sets the tone. Use it to confirm that you know there’s an issue and are working on it. Even if you don’t have all the facts yet, don’t wait. Instead, let people know what’s affected and what to expect next.
Pre-written templates can help you move faster and cover key details like system impact and estimated fix times.
Keep major incident updates coming regularly
Regular updates stop rumors and show you’re in control. It’s helpful to assign one person to manage communication during cyber incidents. This person also keeps track of the timeline and shares updates with everyone involved.
Even short notes like “Still working on it” can help people feel informed. Silence, however, can create doubt or frustration.
Choose one main way to share updates—like email, text alerts, or a status page—and stick to it. In addition to this, tell users where to go for the latest news. This way, they won’t flood your support team with questions, and everyone stays in the loop.
Part IV: Major incident resolution, post-mortem, what comes next
On December 14, 2020, Google users across the globe faced an unexpected disruption. Gmail, YouTube, Google Drive, Google Maps, and even the Play Store suddenly stopped working. Millions of people lost access to their emails, cloud files, navigation, and videos—all at once.
When Google went dark: A lesson in major incident communication
Even Google’s own teams were affected. A spokesperson admitted they couldn’t access email to send a statement. That small detail showed just how far the issue had spread.
Although services came back within a few hours, something else stood out. It wasn’t just the size of the outage updates—it was the silence that followed. For a company trusted by billions, the delay in communication left users frustrated and confused.
This is exactly when strong incident communication matters most.
When things break, your users don’t just want answers. They want to know someone’s listening. They need quick updates, clear facts, and a sense that things are under control.
A simple update can make a big difference. It builds trust, even in tough moments.
Here’s a basic plan that works:
- First, admit there’s a problem and explain how it affects users.
- Then, offer a clear, simple explanation—no tech jargon.
- Next, share the steps your team is taking to fix it.
- Finally, reassure users and show your commitment to doing better.
Outages will happen. But going quiet shouldn’t be an option.
The real test isn’t just how fast you fix the issue. It’s how clearly and confidently you communicate through it.
When every second counts, so does every word—Virima can help
Clear and timely communication during an incident isn’t just helpful—it’s essential. With Virima, you can send updates to the right people, with the right details, at the right time. That means fewer delays and less confusion when every second matters.
Virima makes this possible through smart service mapping and easy-to-understand visualizations. Its automated asset discovery and Virima Visual Impact Display features show near-real-time insights. So, your updates are based on facts, not guesswork.
You don’t need to overwhelm teams with tech jargon or leave customers unsure. Virima helps you send clear updates that make sense. Everyone gets the right amount of context to stay informed, without too much detail.
Even better, Virima keeps your updates accurate and consistent across all channels. It pulls near-real-time data from your ITSM tools, system monitors, and CMDB. This reduces errors and builds trust—no more scrambling for the right info.
(See, How service mapping can improve incident and change management processes)
Using visualizations in stakeholder communications
You’ve probably heard the saying, “A picture is worth a thousand words.” When IT issues happen, people need answers—fast. There’s no time to dig through complex data or long reports. Everyone needs to understand the problem and act quickly.
That’s where Virima’s service mapping and ViVID visualizations come in. They help you clearly see how your IT components, business services, and users connect. With ViVID overlays, you also get a live view of what’s affected, where, and what’s being done to fix it.
Every IT system is part of a bigger picture. It runs through physical locations, business workflows, and many hidden links. Virima shows all of this in a way that even non-technical users can understand. So, everyone stays informed and aligned during any incident.
These visuals aren’t just pretty images—they’re packed with near-real-time insights. You can also spot service health, track changes, and monitor open issues at a glance. This turns your updates from vague guesses into clear, helpful guidance.
Also read: Change management best practices
So, whether you’re explaining what’s down or finding the root cause of a failure, Virima helps you show exactly what matters—clearly and confidently.
Major incident mitigation with visualizations
You can explain incident mitigation steps more clearly with visuals. Instead of sending long status emails, show what’s happening. Let stakeholders see messages like “we’re redirecting traffic to restore partial functionality” or “security controls are active to contain the threat.” These updates become more powerful when backed by near-real-time data.
Virima’s ViVID helps by showing layered impact views. You can see affected services and how they link to changes, alerts, or vulnerabilities. This quick view removes confusion and helps teams make faster decisions in tough situations.
During a major incident, communication does more than share updates. It shapes how others see the situation. It also builds trust and shows that your team has things under control.
With Virima, you’re not just responding—you’re guiding the message. You bring clarity, context, and honesty to every conversation.
See how Virima makes incident communication easier to lead with confidence.
Close the loop on incident chaos—Start with Virima
Virima’s platform does more than just detect issues. It helps you share them clearly and with confidence. Built-in workflows, incident tracking, and service maps keep your team informed. You always know what’s going on and how to act fast.
When problems happen, everyone wants answers. Virima helps you respond with clarity. Here’s how:
- What’s affected? Virima’s service mapping shows exactly which systems are impacted—and who feels the impact.
- What’s being done? Virima’s incident and change tools let you share real-time updates with your team and stakeholders.
- Will it happen again? Virima captures the root cause and keeps track of lessons learned. This prevents future issues and improves response.
There’s no guesswork. No vague updates. Just quick, clear communication—backed by facts.
So when something breaks, your response won’t add to the chaos. With Virima, you lead with confidence and make your team look great every time.
Want to automate your incident updates? Explore how Virima supports near-real-time ITSM incident management or request a demo.
FAQ
What should incident communications be centered around?
When an incident happens, your communication should be clear, quick, and honest. Start by explaining what went wrong in simple terms. Then, share how it affects services and what steps you’re taking to fix it.
Let people know what they can expect next. This approach builds trust and keeps everyone informed without using confusing technical terms.
How often should I update stakeholders?
How often you send updates depends on how serious and long the incident is. If it’s a major issue, send updates every 30 minutes to an hour. You should also update whenever something important changes.
For smaller problems, you can send updates less often. Still, keep them regular so everyone stays informed and feels reassured.
What are the 5 steps to incident response?
The five key steps to incident response are:
- Identification – Detect and recognize the incident.
- Containment – Limit the scope and impact to prevent further damage.
- Eradication – Remove the root cause of the incident.
- Recovery – Restore systems and services to normal operation.
- Lessons Learned – Analyze the incident and improve future responses.
What is the importance of incident communication?
Incident communication matters because it keeps everyone informed and reduces confusion. When you communicate clearly, people know what to expect. This helps protect your reputation and builds trust with customers, employees, and partners.
It also keeps teams working together smoothly to solve the issue fast. With the right updates at the right time, you stay in control.