CMDB asset management vs ITAM: Key differences explained
Imagine it’s audit time again. Your IT team rushes to find reports, check assets, and match configurations. Stress rises as the deadline gets closer, and the systems still feel messy.
Now, picture a better setup. All your records match. Everyone knows what assets you have, who owns them, and how they connect. That’s what happens when you bring CMDB and IT asset management together.
Forrester reports that companies using both systems cut audit prep time by 40%. They also reduce compliance risks by 35%. These results aren’t just stats—they show how easy things become with accurate CMDB asset management data.
So, why does this matter to you? Because understanding CMDB and ITAM—and how they work together—helps you build a smarter IT setup. This blog breaks it all down for you, step by step.
Quick summary before you dive in:
CMDB and asset management each serve a unique purpose, but work best together. CMDB helps you track how IT components connect and support services.
It gives you a clear view of service relationships and dependencies. Meanwhile, ITAM focuses on managing the value, usage, and compliance of your hardware and software. When you combine both, you get better visibility, control, and readiness for audits across your entire IT setup.
What is ITAM (IT asset management)?
The ISO/IEC 19770-1:2017 standard describes IT asset management (ITAM) as a way to get value from digital items. These items help you acquire, process, store, or share digital information. Unlike configuration management, ITAM isn’t just about tracking items. Instead, it brings together several processes, including configuration management, to give more value to your business.
To fully understand IT asset management, you first need to know what an asset is. According to ITIL v3, an asset is anything that helps deliver a service. ITIL 4 expands that and says it’s any useful part that supports an IT product or service. It explains CMDB asset management as the process of planning and managing every stage of an asset’s life.
Best practices for smarter CMDB asset management:
- To manage your IT assets effectively, you first need to classify them. Group them based on their type, use, or risk level. This makes it easier to track each item in your asset register. When you know what you have, you can manage everything with less confusion.
- Next, stay aware of where your assets are. Real-time location tracking helps you avoid loss or misuse. You always know which team or site is using each asset. That way, nothing falls through the cracks.
- As assets age, plan for their end-of-life. Remove anything that no longer works or fits your needs. This further helps you avoid clutter and security risks. It also clears space for newer, more efficient tools.
- At the same time, protect your sensitive data. Set up strict access controls on your systems. Only the right people should get the right information. This reduces the chance of leaks or cyberattacks.
- Keep an eye on your spending, too. Use built-in reports to track what each item costs. You’ll see where the money goes and find ways to cut waste. This helps your budget go further.
- Don’t forget your cloud services. Track how much you spend on licenses, storage, and data transfer. With clear insights, you can adjust usage or costs as needed. That’s key to staying efficient in the cloud.
- Understanding the distinction between CMDB asset management and ITAM is the conceptual foundation. For a practical implementation example, the Virima-Ivanti partnership demonstrates how CMDB asset management works in practice, with Virima’s discovery populating CI data into the Ivanti CMDB while Ivanti’s ITSM workflows consume that data for incident, change, and configuration management.
Also read, 9 ways to declutter your ITAM tool
What is a CMDB?
If you’re wondering what is CMDB, it’s short for Configuration Management Database. It is also called service asset and configuration management (SACM), which helps you control your IT assets. It ensures that the right information about those assets is available when and where you need it. This approach keeps the CMDB database streamlined and ensures seamless service operation by monitoring and recording all activities. The CMDB’s operational value becomes most visible during incident response. A practical guide on connecting ITSM incident management CMDB workflows shows how CI relationships, dependency data, and configuration history accelerate root cause identification in ways that financial-focused ITAM data alone cannot support.
Unlike IT asset management (ITAM), which helps you make strategic decisions, configuration management focuses more on operational control. ITAM uses the data, but configuration management keeps that data accurate and up to date.
You’ll need details on how to set up each asset and how they connect to each other. In configuration management, you call every asset you track a Configuration Item (CI). These are things like hardware, software, documents, or anything else that supports your IT services.
According to the ISO/IEC 20000-1:2018 standard, a CI is something you must control to deliver services. These items often rely on each other, so understanding their relationships is key. With the right setup, you gain visibility and control over your entire IT environment.
Read more about CMDB discovery here.
How to keep your configuration items up-to-date:
Here’s a simple guide to help you stay on top of your CIs:
- Start by asking, “What hardware or software is currently in use within my environment?” This is your first step—identifying your CIs.
- Once you identify each CI, ensure you document it properly and add it to your configuration management system.
- When you need an update, revise the existing CI’s details rather than starting from scratch.
- If a CI is no longer relevant or in use, the team should remove it from the system.
- After every update, confirm that the team accurately revised the CI information.
- Lastly, consider the potential impact if a particular CI were to fail. Use this scenario to assess how it would affect your services.
Read more about CMDB asset discovery.
Why do you need both ITAM and CMDB?
If you’re wondering whether a CMDB can replace ITAM, here’s why you need both.
IT Asset Management (ITAM) and configuration management each play a key role. However, they are even more effective when used together. A solid CMDB asset management gives real-time, accurate data on asset relationships, which ITAM needs to work well.
So, do you need both? The answer is yes. Without CMDB integration with ITAM, you might miss the context needed for complete asset and service management.
Picture this: a laptop is the asset, while its software or operating system are configuration item (CI). People buy the laptop, use it, and eventually replace it. But the software (like your operating system and apps) outlasts the physical laptop.
ITAM tracks the laptop for depreciation, warranty, and support. On the other hand, you track the OS or software as a CI in the CMDB. This, in turn, helps with service delivery and change management. The CI could represent services like email or an app, with a lifecycle longer than the laptop itself.
This distinction shows ITAM tracks physical assets like laptops, while CMDB manages services and configurations like operating systems. It’s not about the overlap between the two systems. Instead, it’s about knowing each tool’s role in managing your IT environment effectively.
Working together in practice
To make CMDB asset management truly valuable, CMDB and ITAM need to work together, not in isolation. ITAM tracks assets’ lifecycle, cost, and compliance. Meanwhile, CMDB maps how those assets support IT services as configuration items (CIs). By syncing inventories, you ensure accurate data and avoid duplication.
Streamlining asset data with syncing
Instead of manually creating asset records in the CMDB, link existing ITAM assets to the correct CIs. This makes it easy to pull in asset details, such as warranty status or ownership, when needed. This approach keeps the CMDB asset management streamlined and avoids cluttering it with irrelevant information.
Consider contracts. Storing contract documents and key dates in the CMDB asset management may require heavy customization. It’s better to use an ITAM or contract lifecycle management system for that. However, linking these contracts to the related CIs in the CMDB keeps the service context intact.
Enhancing service dependency mapping
Mapping service dependencies in the CMDB also becomes clearer with ITAM data. For instance, link a CI like a virtual machine in the CMDB to its ITAM record directly. This record contains license details, cost information, and ownership data. This, in turn, adds useful context for better decision-making and service management.
This process strengthens your CMDB dependency mapping, making it easier to trace and manage service links.
Think of it like a transit system. The CMDB tracks buses, routes, and schedules, while ITAM tracks the buses’ history, insurance, and maintenance records. By integrating CMDB and asset management, you assign, monitor, and maintain each “bus” correctly.
Integrating both systems preserves their strengths. The CMDB provides actionable service context, while ITAM adds detailed lifecycle management information. This collaboration supports ITIL-aligned change management, incident resolution, and long-term cost savings.
Read more about IT asset lifecycle management.
Adapting to modern IT environments
In 2025 and beyond, businesses face growing pressure from cloud expansion, remote work, and stricter regulations. The rise of SaaS, IoT, and cloud infrastructure creates new challenges that demand more agile CMDB asset management.
- Cloud resources change fast. Because of this, manual tracking becomes hard. That’s why you need ITAM tools to track usage and costs. At the same time, your CMDB should show how each cloud service supports your business.
- SaaS apps often sneak into your network without IT knowing. If you don’t track them, you’ll face gaps and risks. So, track licenses with ITAM and link their service paths in your CMDB. That way, you keep your systems safe and compliant.
- IoT devices also create tracking challenges. They don’t always fit into regular asset systems. Your ITAM might just log the basics. But your CMDB should still show how these devices connect to key services or networks.
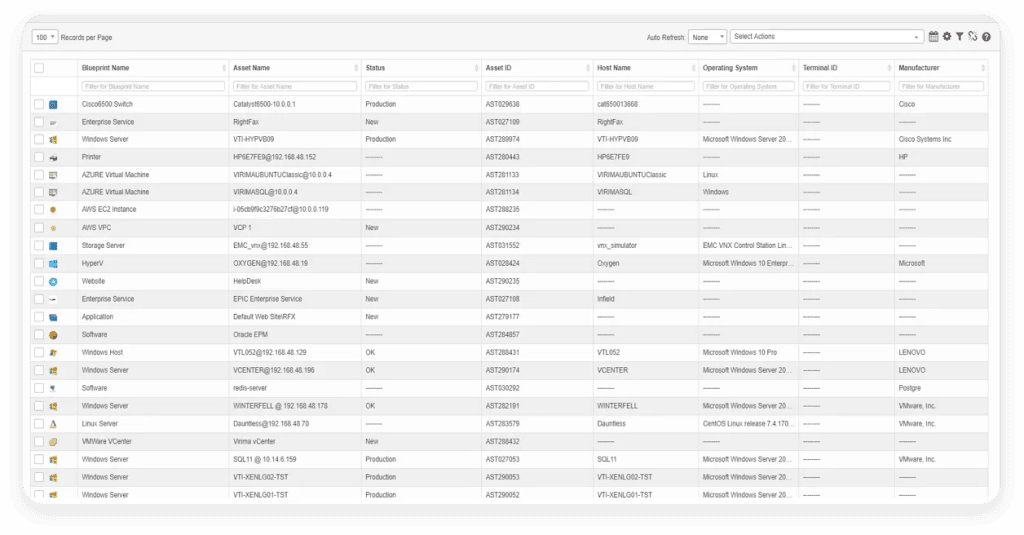
To manage all this, many teams use IT discovery and CMDB auto discovery tools. These tools sync data between ITAM and CMDB platforms. With Virima, you gain near real-time views into assets, service links, and system changes—without the chaos.
See how Virima simplifies CMDB asset management with automated asset discovery.
Impact in action:
A large multinational client integrated their CMDB with Virima’s ITAM solution. As a result, they saw a 30% faster audit preparation time compared to previous years. This made it easier for their team to track and verify every asset. In turn, their audits became quicker and more efficient.
Full audit history and versioning of all configurable items (CI) updates from Virima CMDB
Understanding SAM, ITAM, and CMDB: It’s not about “versus”
When exploring CMDB vs asset management, it’s easy to think you must choose one over the other. But in reality, they serve different—yet complementary—purposes.
| Category | SAM (Software Asset Management) | ITAM (IT Asset Management) | CMDB (Configuration Management Database) | Asset Register |
| Focus | Software licensing, usage, and compliance | Lifecycle and financial management of all IT assets | Tracking configuration items and their relationships within IT services | A simple record of all physical and digital assets owned by the organization |
| Scope | Software only | Hardware and software assets | Hardware, software, services, documentation, and dependencies | Typically focuses on physical assets (hardware, equipment, etc.) |
| Primary goal | Ensure license compliance and optimize software costs | Track ownership, location, cost, and lifecycle of IT assets | Support change, incident, and problem management through accurate configuration data | Maintain an up-to-date inventory of assets for auditing and operational tracking |
| Data tracked | Installations, license keys, usage metrics, vendor agreements | Purchase date, warranty, location, user, depreciation | Dependencies, relationships, versions, and current state | Asset identification (e.g., serial numbers), purchase date, and location |
| System of record for | Software licenses and compliance | Entire IT asset base | IT service components and their relationships | Physical assets, such as laptops, furniture, and IT hardware |
| Typical tools | Flexera, Snow Software, ServiceNow SAM | ServiceNow ITAM, Virima, Lansweeper | ServiceNow CMDB, BMC Atrium, Virima CMDB | Manual registers, Excel sheets, or basic inventory management tools |
| ITIL relevance | Supports ITIL financial and compliance processes | Supports ITIL asset and financial management | Core to ITIL service management (change, incident, problem, etc.) | May support ITIL asset management, but typically not as comprehensive |
| Interrelationship | Subset of ITAM | Broad management layer that includes SAM | Consumes data from ITAM and SAM to form accurate CI records | A foundational tool that feeds into ITAM and CMDB systems by providing asset inventory |
Also read, What are the differences between IT asset management and inventory management?
What types of assets can CMDB and asset management manage?
When managing IT assets and configuration items, you include many different types. Anything used to deliver an IT service falls under the scope of IT asset and configuration management. However, some organizations limit their scope, focusing only on physical assets and configuration items like hardware and network components.
It’s essential to balance the risks and rewards of managing assets. You can do this by adjusting the management level for different types of assets. Some assets that are often prioritized in CMDB asset management and configuration management include:
- Hardware: Desktop computers, servers, network equipment, and storage devices.
- Software: Applications, operating systems, and databases.
- Portable devices: Mobile devices like laptops, smartphones, and tablets.
IT services rely on these crucial assets, so we should manage them carefully. However, focusing solely on these assets may lead to managing more components than you can handle. To avoid this, both IT asset management (ITAM) and configuration management should use a risk-based approach. For example, hardware like cables or internal network cards might not need as much focus.
This clear distinction of CMDB vs asset management helps you prioritize the right elements for your IT environment.
Manage your assets better with Virima
Effective configuration management is essential for IT asset management. It helps maximize the availability of services and reduces risks. Proper management also saves your organization money by identifying and removing unused IT assets. Moreover, it supports compliance with regulations.
Virima provides a comprehensive set of tools and solutions for IT management challenges. With Virima, you can improve the health of your IT environment. You’ll also benefit from enhanced configuration management, including your CMDB and asset management.
Virima’s IT Asset Management (ITAM) and Configuration Management Database (CMDB) solutions maximize the value of your ITSM investments. They offer flexible IT discovery options to collect data from both physical and virtual infrastructures.
As a leader in IT Asset Management and CMDB solutions, Virima supports multi-cloud environments. With automated dependency and service mapping, you’ll see faster, more efficient results.
Virima also offers a full-featured CMDB with the Virima Visual Impact Display (ViVID). Plus, it integrates deeply with popular ITSM platforms. This makes managing IT services simpler and more efficient.
For Atlassian customers, that integration translates into a fully populated Jira service management CMDB without the usual schema and maintenance overhead. A Jira service management CMDB built on Virima combines Virima’s ITAM lifecycle data with live CI relationships inside Jira, so lifecycle facts from ITAM — warranty, ownership, cost and service context from the CMDB show up in the same record. Jira users get one view for asset-level and service-level decisions, which is the entire point of running ITAM and CMDB together.
To learn more about Virima’s IT and service management solutions, request a demowith Virimatoday!
FAQs: Your questions answered
1. What is a CMDB, and how does it support asset management?
A CMDB (Configuration Management Database) is a central place to store information about your IT assets. In asset management, it helps track hardware, software, and their connections. The CMDB does more than list assets—it shows how each item interacts within your IT services. This makes it easier for your team to manage and secure these assets.
2. How to get started with CMDB for asset management?
To start using a CMDB, follow these steps:
- Define what to track: Identify the assets and services you need to manage.
- Collect data: Gather configuration information about your assets, including hardware, software, and connections.
- Map dependencies: Understand how assets work together and affect each other.
- Choose a tool: Pick a CMDB solution that fits your needs (like ServiceNow or Virima).
- Automate discovery: Use an asset management tool to automatically update asset status in the CMDB.
- Set up rules: Create processes to keep your CMDB data accurate, with regular audits.
3. Can a CMDB replace an asset register in asset management?
A CMDB can replace an asset register, but it offers much more. An asset register tracks basic asset details like serial numbers and locations. A CMDB goes beyond this by showing how assets interact within your IT services.
It gives detailed information about each asset’s configuration and its impact on the system. So, while a CMDB can manage asset data, it provides a fuller view of your IT environment.
4. How can a CMDB help with IT asset tracking in large organizations?
An asset inventory is a list of assets, usually focused on physical items like computers or servers. It includes basic information like serial numbers and locations. A CMDB, however, provides more depth.
It tracks more than just assets. It also records how you configure them, their dependencies, and their role in IT services. This deeper insight makes tasks like change management and incident resolution easier. With this, you get a clearer view of your IT environment.
5. What’s the difference between a CMDB and an asset inventory?
An asset inventory is simply a list of assets, usually focused on physical items like computers or servers. It includes basic details such as serial numbers and locations. A CMDB, however, provides much more.
Moreover, it tracks assets, their configurations, dependencies, and how they support your IT services. This deeper insight helps with tasks like change management and incident management. Altogether, it gives you a complete picture of your IT environment.
6. How to implement both ITAM and CMDB?
Integrating IT Asset Management (ITAM) with a Configuration Management Database (CMDB) improves visibility, compliance, and efficiency. Here’s how organizations typically integrate ITAM with a CMDB:
- Define integration scope: Start by identifying which IT assets and configuration items (CIs) should be integrated. Focus on the critical assets and services that affect your business operations directly.
- Select compatible tools: Choose tools that support CMDB integration with ITAM. Make sure they can synchronize data smoothly, like linking asset records with the corresponding CIs.
- Map data fields: Align data fields between ITAM and CMDB systems to maintain consistency. For instance, map asset identifiers to CI identifiers and ensure attributes like ownership and status match.
- Automate data synchronization: Set up automated discovery and synchronization processes to keep asset and configuration data up-to-date. This reduces errors and ensures data accuracy in real time.
- Establish governance and ownership: Assign clear roles for both ITAM and CMDB data. Define responsibilities to maintain data integrity and stay compliant with company policies.
- Integrate with IT Service Management (ITSM): Link ITAM and CMDB data to ITSM processes. It includes change, incident, and problem management. This helps you understand how asset changes affect services.
- Monitor and optimize: Regularly audit the integration to find areas for improvement. Adapt your processes to business needs and technology changes.