Agent-based vs. agentless discovery: which is best for your business?
When it comes to IT discovery, there are two main approaches. These are agent-based and agentless methods. Many companies struggle with this choice. The debate of agent-based vs. agentless discovery depends on business needs, IT setup, and resources.
A quick overview of agent-based vs. agentless discovery systems
TL;DR – Key points:
- Agent-based discovery requires installing small programs (agents) on each device.
- These agents collect system details and send them to a central server.
- It provides deep and continuous monitoring insights into device performance and usage based on the data collected from endpoints.
- Agentless discovery skips installation and works through network traffic checks or APIs.
- It scans devices directly, pulling data such as location and basic asset information and features and data collected from active IoT devices.
- It is faster to deploy and easier to maintain but less detailed.
- The choice between agent-based vs. agentless discovery depends on how much detail and control you need and understanding the pros and cons of each method.
What is agent-based discovery?

Agent-based discovery
To begin, agent-based discovery relies on installed agents. These agents collect data about the device and send it back.
In addition, this method is helpful when you need to monitor many devices. After setup, agents run on their own.They provide continuous monitoring updates with little work from administrators,enabling better monitoring and protection of systems.. These agents are part of agent-based security solutions, offering detailed system visibility.
What is agentless discovery?
Agentless discovery
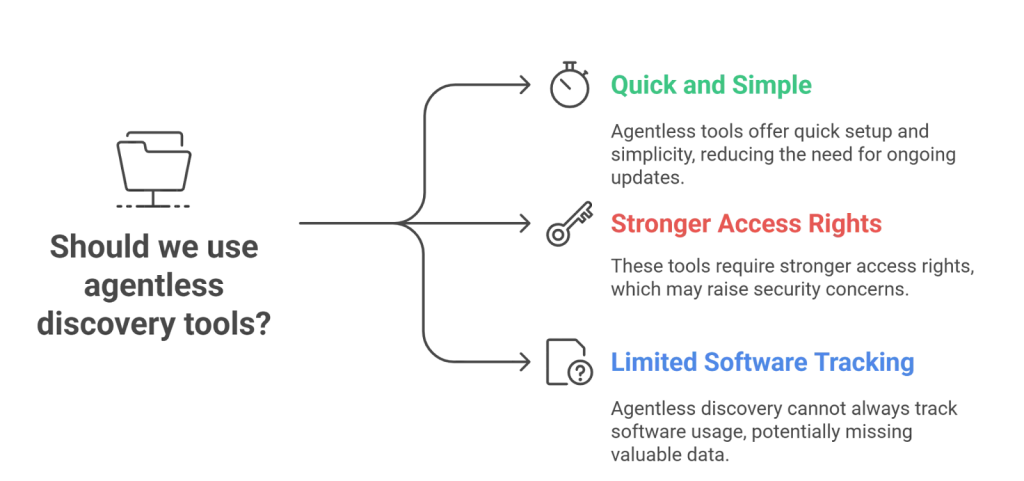
On the other hand, agentless approach skips installation. It uses basic network traffic scans to find and check devices.
Moreover, a central server runs these scans. It pulls asset information about systems and applications directly. While this avoids agent maintenance, it needs stronger access rights. Also, it cannot always track how software is being used ,especially across IoT devices.
For many teams, agentless discovery tools are a good fit. They are quick, simple, and reduce the need for ongoing updates.
Agentless vs. agent-based discovery
Now, let’s compare. Both methods identify devices and gather useful data. Yet, the choice of Agent-based vs. agentless discovery depends on how much detail you need.
For example, agent-based discovery collects deep system details such as memory, CPU, or storage use. Meanwhile, the agentless approach provides faster scans but with fewer details.
Here’s a simple comparison:
| Category | Agent-based | Agentless |
| Visibility | Offers rich, detailed insights. | Limited, less frequent data. |
| Deployment | More complex, needs setup. | Quick, no extra software. |
| Information | Tracks usage and performance. | Uses checks for fast insights. |
| Infrastructure | Covers IoT, VMs, servers, and more. | Works widely but less detailed. |
Which discovery option works best for your business?

Agent-based vs agentless discovery
1. Security
First, think about security. Agent-based discovery offers strong visibility and can monitor systems in real time. Yet, managing agents can be complex.
By contrast, an agentless discovery tool is easy to use. It checks devices without extra software. Still, it may miss hidden assets, which can create risks. Strong monitoring and protection policies can reduce those risks.
Modern agent-based security solutions help address this gap by providing real-time alerts and automated responses.
2. Deployment
Next, look at deployment. Agent-based discovery takes longer. It requires setup and maintenance.
Meanwhile, agentless discovery is faster to roll out. But it depends on network traffic quality. In weak networks, results may be less reliable.
3. Resource use
Also, consider resources. Agent-based discovery uses device power, such as memory and CPU. In comparison, agentless discovery tools use network traffic bandwidth instead.
4. Accuracy and scale
Finally, accuracy and scale matter. Agent-based discovery is precise and works well in large setups. However, installing agents across many sites takes effort.
On the other hand, agentless methods scale quickly. Yet, they may not be as accurate because scans are less frequent.
| Consideration | Agent-Based Discovery | Agentless Discovery |
| Security | Strengths: Real-time monitoring, detailed visibility. Weaknesses: Complex to manage agents; agents can be exploited if not secured. | Strengths: Easy to deploy, smaller attack surface. Weaknesses: May miss hidden assets; no real-time monitoring. |
| Deployment | Strengths: Granular control and customization. Weaknesses: Time-consuming installation and ongoing maintenance. | Strengths: Fast rollout, no software required on devices. Weaknesses: Depends on network quality; firewalls can block scans. |
| Resource Use | Strengths: Local processing reduces network strain. Weaknesses: Uses device CPU and memory, especially older systems. | Strengths: No device performance impact. Weaknesses: Consumes network bandwidth; may slow traffic. |
| Accuracy & Scale | Strengths: High accuracy, detailed insights, strong in large/complex setups. Weaknesses: Hard to deploy and manage across many sites. | Strengths: Scales quickly, simple to expand coverage. Weaknesses: Less accurate, may miss assets. |
Common IT pain points with discovery approaches
From an IT manager’s perspective, discovery often brings challenges. Choosing between agent-based vs. agentless discovery can feel overwhelming.
Here are some real-world pain points:
- “I can’t install agents on legacy systems or unmanaged endpoints.”
- “Maintaining agents across hundreds of servers takes too much time.”
- “Our agentless scans miss important usage data that security teams need.”
- “Bandwidth spikes during discovery scans disrupt normal operations.”
- “We need visibility across cloud native, on-premises, and IoT — but no single approach covers all.”
These issues highlight why many IT leaders now look for hybrid solutions instead of choosing only one method.
Next, let’s match discovery approaches to real IT environments. The right choice often depends on context.
- Highly secure networks
Use agent-based discovery. Agents run locally, so fewer ports stay open. This reduces security risks. - Remote work environments
Choose agentless discovery tools. They connect over standard protocols like SNMP, WMI, or SSH. No endpoint installation is needed, which is ideal for unmanaged laptops. - Hybrid infrastructure
Combine both methods. Use agents in your core data centers for deep metrics. Use agentless scans for cloud native VMs, containers, or branch offices where installing software is impractical.
In short, agent-based vs agentless isn’t a “one-size-fits-all” decision. It’s about aligning the method with your network setup.
Technical considerations IT managers must know
Now, let’s get precise about technical details. These factors often influence the decision between agent-based vs. agentless discovery.
- Protocols:
- Agentless methods rely on SNMP, WMI, and SSH.
- Agents communicate directly with the management server, bypassing open-port requirements.
- Bandwidth:
- Agent-based discovery uses minimal network traffic since agents run locally.
- Agentless scans push more traffic, which can strain networks during peak hours.
- Operating system compatibility:
- Agents support Windows, Linux, Unix, and macOS.
- Agentless methods may struggle with older systems or non-standard devices.
- Scalability:
- Agent-based is accurate but harder to manage at a massive scale.
- Agentless scales faster but with lower precision.
Understanding these details ensures IT managers can choose a model that won’t cause surprises in production.
Virima Discovery: Real capabilities in action
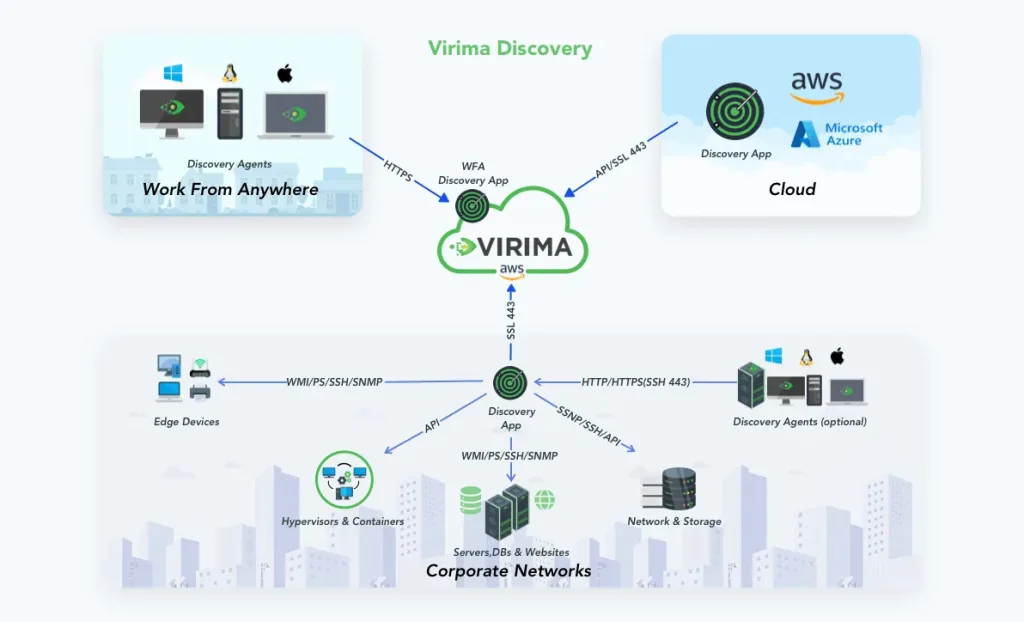
Virima Discovery in action
Finally, let’s look at how Virima Discovery addresses these challenges.
- Hybrid discovery model: Virima supports both agent-based and agentless IP-based scans. You get deep insights and fast coverage at the same time.
- Broad compatibility: It works with Windows, Linux, Unix, and macOS. Legacy systems and modern cloud native platforms are both supported.
- Efficient bandwidth use: Agent-based discovery minimizes network traffic load. Meanwhile, Virima’s optimized agentless discovery tools reduce scan overhead compared to traditional solutions.
- Scalable design: Its multi-tenant architecture lets you scale up or down without extra licensing costs.
- Cloud integration: Virima connects with AWS and Azure to automatically detect new asset information and cloud native assets.
IT teams using Virima report up to 40% faster discovery times when combining agent-based and agentless methods. This helps them keep asset inventories accurate while reducing manual effort.
With these capabilities, Virima turns the agent-based vs. agentless discovery debate into a flexible, “best of both worlds” solution.
Virima Discovery – The best of both worlds
Luckily, you don’t have to pick just one. Virima Discovery offers both. It combines agent-based scanning for detail with agentless discovery tools for speed.
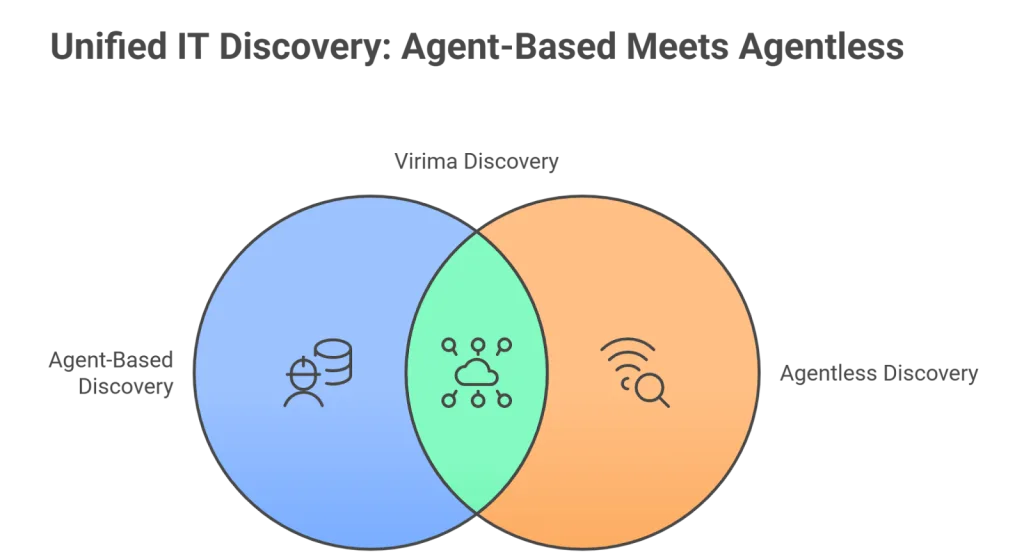
Virima IT Discovery – the best of both worlds
With Virima, you can detect thousands of assets in cloud and on-premises setups. It works across Windows, Linux, Unix, and Mac.
Most importantly, Virima scales with your business. It avoids extra licensing costs and supports IoT, cloud, and hybrid systems through agent-based security solutions.
In short, the choice of agent-based vs agentless discovery depends on your IT landscape. But with Virima, you get the strengths of both while avoiding their downsides.
Ready to simplify IT asset management? Discover how Virima’s hybrid discovery solution combines continuous monitoring, asset information, and agent-based security solutions to give you complete visibility and control.
FAQs: Agent-based vs. agentless discovery
1. What is the difference between agent-based and agentless discovery?
Agent-based discovery installs software agents on each device for deep monitoring. Agentless discovery uses protocols like SNMP, WMI, or SSH to scan devices without software installation.
2. Which is more secure: agent-based or agentless discovery?
Agent-based discovery offers real-time monitoring and stronger visibility but requires careful management of agents. Agentless discovery reduces the attack surface but may create blind spots if devices are hidden or offline.
3. What are the benefits of agentless discovery tools?
Agentless discovery tools are easy to deploy, quick to scale, and don’t consume device resources. They are ideal for remote work environments or when IT teams want fast visibility without installing software.
4. Can I use both agent-based and agentless discovery together?
Yes. Many IT managers choose a hybrid approach. Agents provide detailed insights for critical systems, while agentless scans cover cloud, IoT, and remote devices. Solutions like Virima Discovery make this possible.
5. Which is better for hybrid or cloud environments?
Agent-based vs. agentless discovery is not an either/or choice in hybrid environments. Agentless discovery works best for cloud VMs and containers, while agents provide deeper metrics in on-premises data centers.