Active vs passive IT asset discovery: when to use each
You just got an alert: 7 devices are online that you don’t recognize. One is a connected appliance in the break room. Another is a laptop that hasn’t been used since 2021.
If you manage assets and IT infrastructure, we bet you’d relate to it hard.
In fact, a survey revealed that nearly half of IT leaders (44%) admit they can’t see all the devices on their networks. Mostly still rely on spreadsheets to track assets that cost thousands.
Shadow IT, IoT devices, and lab or smart equipment often slip under the radar.
Without proper IT discovery, teams waste hours fumbling, unsure which devices are connected devices, safe, or lost.
IT asset discovery tools with capabilities like active asset discovery solve this problem by identifying all devices, sending real-time monitoring, and making management far easier.
But there’s more to IT discovery tools.
In this blog, we will highlight various types of asset discovery tools and explain how active discovery tools and passive asset discovery tools differ.
| TL;DR Discovery probes devices; passive discovery listens silently. Together they reveal your IT landscape. Active discovery: Uses probes (ping, SNMP, WMI, SSH), credentials, or agents to query devices directly. Outcome: rich configuration and software details and asset data. Passive discovery: Uses SPAN/TAP ports, flow data, syslogs, IDS logs to passively detect devices. Outcome: safe, broad coverage without network disruption and continuous realtime monitoring. Hybrid discovery: Combines both, passive for a constant baseline, active for enrichment. |
What is IT asset discovery?
IT Asset Discovery is the process of identifying assets and listing all the IT devices, software, and cloud services in an organization so they can be managed properly.
It covers:
- On-premises servers, endpoints, and network gear
- Cloud workloads and SaaS (IaaS, PaaS, SaaS)
- Remote endpoints (hybrid workforce laptops)
- Containerized workloads
- IoT and OT/ICS devices
Without asset discovery, it’s like trying to fix a leaking pipe in a building without knowing which floor it’s on, or even if it exists. You can’t patch it, monitor it, or secure it if you don’t know it’s there.
The goal is to know what assets exist, where they are, and how they’re performing to prevent IT security gaps using complete asset data from discovered assets.
Imagine your organization just added a batch of remote laptops for a hybrid workforce. If IT doesn’t have an asset discovery process in place, some laptops might never get security updates, leaving gaps that attackers could exploit.
Now, let’s break down active vs. passive asset discovery to understand how they function.
Active vs passive asset discovery
Quick note: There are two main ways to find these assets: active and passive discovery. Each has its own strengths, weaknesses, and real-world use cases. Both methods have trade-offs: active gives detailed, real-time insights but may impact the network including load; passive is safer for sensitive environments but may take longer to capture all assets.
Active discovery
TL;DR: Actively queries your devices for deep insights, but can introduce monitors network traffic load.
Active discovery, sometimes called standard asset discovery, involves software actively polling devices across a network including various endpoints. This could be as simple as a classic ping-and-response scan, or more sophisticated queries that log into devices to pull an inventory of installed software, applications, and configurations- resulting in richer asset data about connected devices.
Pros:
- Discovery gives a detailed, near-real-time view of devices on the network..
- Great for small to medium network devices where the impact of scanning is minimal.
Cons:
- It can consume network bandwidth, which may slow sensitive or time-critical systems. Some devices, particularly in operational or high-availability environments, may not respond well to active scans.
Despite these drawbacks, active asset discovery suits various large-scale environments where keeping track of devices and systems is critical.
Typical uses include:
- Enterprise IT networks: Large corporations scan subnets to inventory servers, laptops, and virtual machines, ensuring all endpoints are patched.
- Healthcare: Hospitals actively query imaging equipment and patient monitoring devices to verify software versions and firmware updates.
- Cloud and hybrid IT: SaaS companies scan virtual machines and containers across AWS, Azure, and GCP to detect orphaned resources and ensure compliance.
- University campuses: IT teams actively scan lab computers and Wi-Fi-connected student devices to assign network policies.
- Retail POS networks: Retail chains scan POS terminals and handheld devices nightly to maintain PCI DSS compliance.
In short, active discovery provides rich device insights but requires careful management of network impact. Moving further ro passive discovery.
Read Virima’s healthcare case study, which it provided visibility to the hospital’s 7,000 server configurations and 2,000 applications.
Passive discovery
TL;DR: Listens quietly for safe, continuous visibility but with less detail per device.
Passive discovery, by contrast, primarily monitors network traffic that devices already generate on the network, including logs such as syslogs. Instead of actively sending requests, it observes and records this information, gradually building an inventory over time without generating additional network traffic.
This approach aligns closely with CIS controls by minimizing scanning risk and providing continuous IT asset visibility without disrupting operational systems. For example, it is especially valuable in environments where active scanning could pose risks or disrupt ongoing operations.
The benefits of passive discovery include:
Pros:
- Avoids network congestion or disruption.
- Can detect network devices that rarely respond to active scans.
- Works with historical data, so even devices missed in the past can be discovered later.
However, there are some limitations. Passive discovery requires devices to generate traffic or logs; without them, detection becomes difficult. Additionally, it can take longer to build a comprehensive inventory because data accumulates gradually.
For example, in a manufacturing plant, passive discovery can capture syslogs from PLCs or HMIs. Even “no-touch” devices that cannot be actively scanned are identified safely, without opening any connectivity between IT and operations.
Typical use cases include:
- Manufacturing plants where fragile PLCs and HMIs require careful monitoring.
- Hospitals are monitoring syslogs from imaging devices for asset tracking.
- OT lines where active scans could disrupt production, making passive discovery the safer choice.
In summary, passive discovery offers a safe, continuous way to monitor devices, especially in sensitive or operationally critical environments, though it requires patience and reliance on device-generated data.
Active vs passive IT asset discovery – which is better for large networks
Naturally, keeping track of every device in a large network is no small feat.
When deciding between active and passive IT asset discovery, understanding their respective strengths helps determine the best approach.
Active discovery actively scans the network to find and inventory devices in real time, making it great when you need a detailed snapshot across a sprawling IT landscape. On the other hand, passive discovery quietly monitors traffic and logs to identify devices without disrupting operations, which makes it ideal for sensitive or high-availability systems.
Therefore, for sprawling enterprise networks, the best practice is often to combine both methods—using passive monitoring for sensitive systems to ensure operational safety, while applying active scanning in areas where network load permits. This hybrid approach provides both comprehensive coverage and minimizes risk, striking the right balance between visibility and stability.
Comparing active and passive IT asset discovery: key considerations
Choose the asset discovery approach that aligns with your environment’s needs by evaluating critical factors like scope, network impact, data freshness, credential requirements, and security risks.
Discovery scope
To begin with, active discovery can reach virtually all devices on the network, providing a comprehensive inventory. In contrast, passive discovery only identifies devices that generate traffic or logs. This makes passive discovery ideal for sensitive environments but means it may miss offline or dormant devices.
Blind spots
Moreover, active scans can miss devices that are offline or actively blocking scan attempts. Meanwhile, passive discovery depends on devices communicating or generating logs; consequently, some endpoints may remain undetected unless additional monitoring or occasional active scans supplement the process.
Network impact
When it comes to network impact, active scans generate traffic that can slow down networks—especially in high-availability systems like ICS or critical enterprise environments. On the other hand, passive discovery avoids this entirely by quietly listening to network flows and log streams without adding extra load.
Data freshness
Regarding data freshness, active discovery provides real-time data during each scan, offering immediate insights into device configurations and status. Conversely, passive discovery is event-driven and can leverage historical logs to identify devices that were previously missed or offline, enriching the overall visibility.
Credential needs
Another key difference lies in credential requirements. Active discovery often needs credentials to gather detailed configuration and software information, whereas passive methods do not require credentials because they rely solely on observing existing traffic or log data.
Agentless vs agent-based options
In terms of deployment, active discovery can function with or without agents depending on the depth of data needed. Generally, passive discovery is agentless, relying on network sensors, SPAN/TAP ports, or centralized log collection.
Cloud & saas coverage
Furthermore, active discovery can integrate with cloud APIs and agent-based tools to inventory IaaS, PaaS, or SaaS environments. In comparison, passive discovery monitors flow logs, syslogs, or other telemetry to detect cloud usage and shadow IT activity.
Security risk
On the security front, active scans can sometimes trigger alerts, generate vulnerabilities, or expose configuration weaknesses if misconfigured. Passive discovery, however, minimizes risk by observing rather than probing devices.
Cost and effort
When considering cost and effort, active discovery usually involves more setup, ongoing maintenance, and credential management, making it medium to high in resource demand. Passive discovery is generally lower effort, focused on sensor deployment and log ingestion, though ongoing monitoring remains necessary.
CMDB mapping
Finally, for CMDB mapping, active discovery can feed configuration management databases with rich, detailed information directly, making it ideal for governance and compliance purposes. Passive discovery can also contribute to CMDBs but typically relies on log-based asset creation, which may require additional correlation and enrichment to reach the same level of detail.
With these factors in mind, here’s a quick side-by-side comparison to highlight their differences and help you decide which method or combination fits your organization best.
Active vs passive: side-by-side comparison
Below, we’ve compared active vs passive discovery across critical parameters to help you choose the right tool for your environment.
| Parameter | Active | Passive |
| Discovery scope | All reachable devices | Devices generating traffic/logs |
| Blind spots | Devices are offline or blocking scans | Devices not communicating, no logs generated |
| Network impact | Medium–High (scan traffic) | Minimal |
| Data freshness | Real-time during scan | Event-driven, can include historical logs |
| Credential needs | Often required for detailed config data | Not needed |
| Agentless/Agent | Both options | Typically agentless |
| Cloud & SaaS coverage | Integrates with APIs and agent-based discovery | Logs, flow monitoring |
| OT/ICS Fit | Limited—risk of disruption | High—safe in sensitive networks |
| Security risk | Medium—scans may trigger alerts | Low |
| Cost/effort | Medium–High (setup, maintenance) | Low–Medium (sensor deployment, log ingestion) |
| CMDB mapping | Direct mapping is possible with detailed info | Can feed CMDB via log-based asset creation |
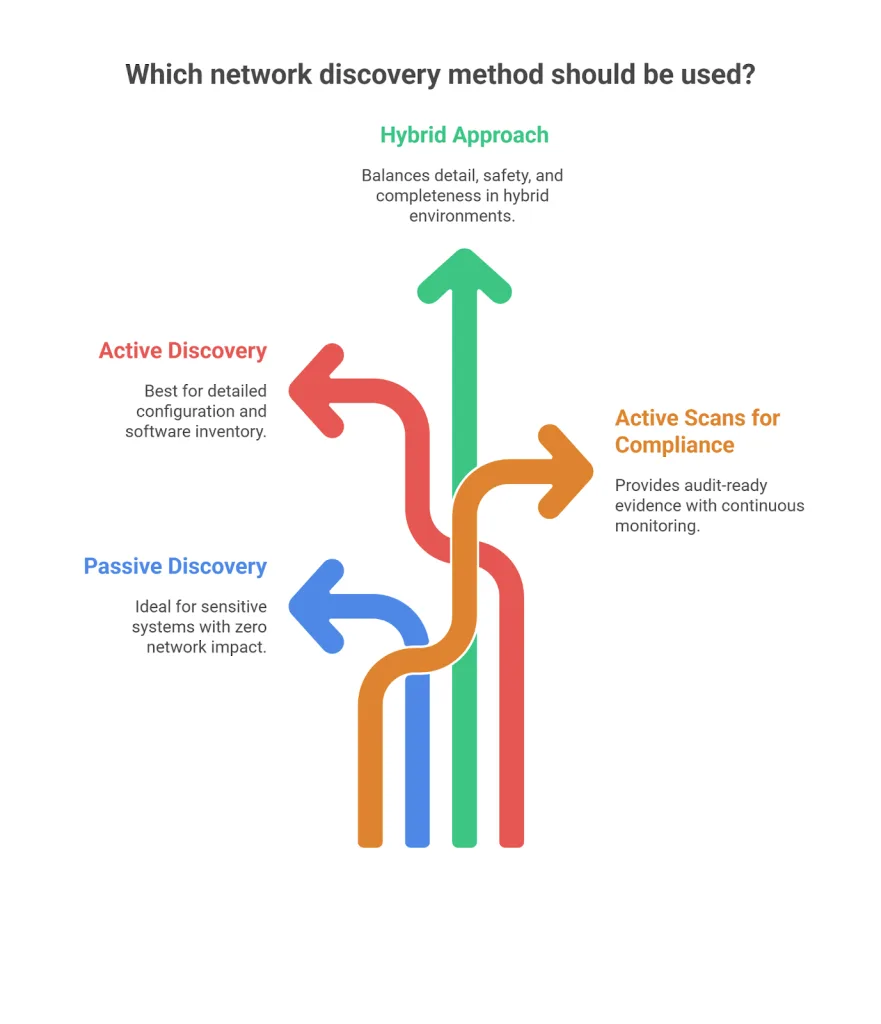
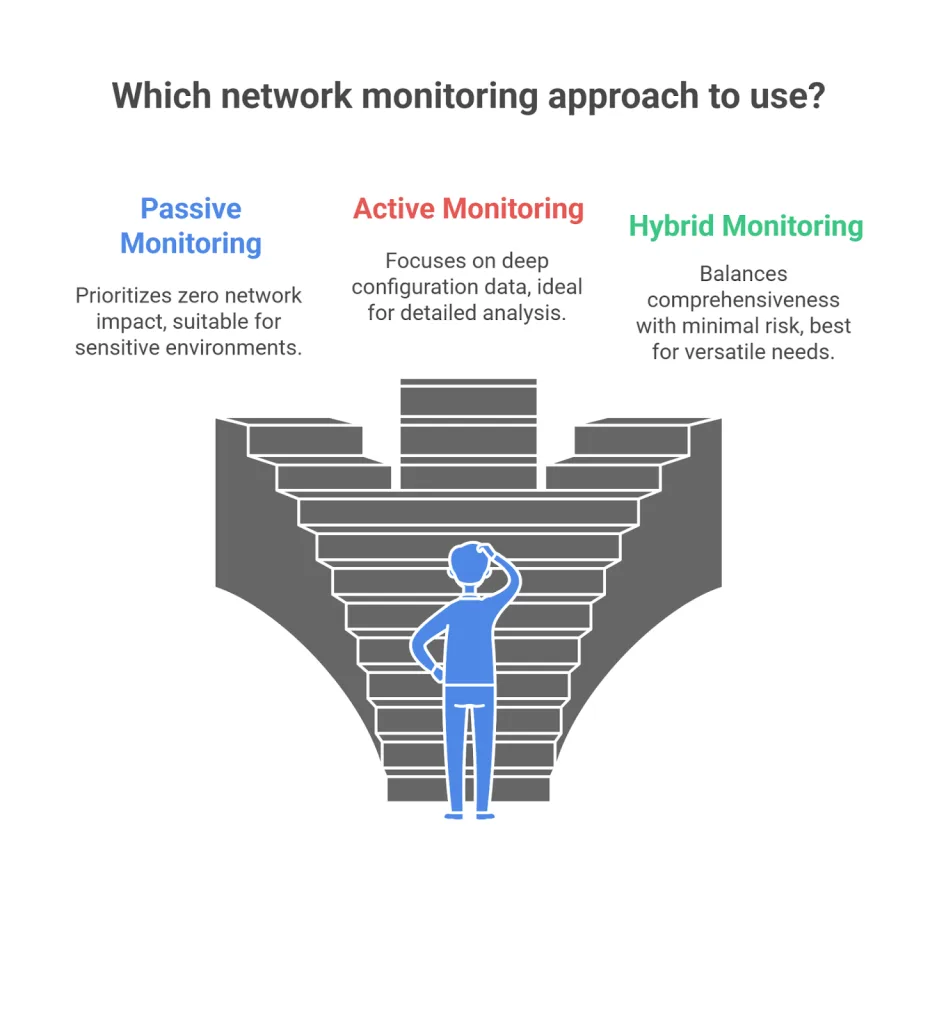
Decision framework: when to use what
Choosing the right asset discovery method comes down to what matters most: avoiding network disruptions or getting detailed device info. If you want to keep things quiet and risk-free, passive discovery quietly listens in without adding traffic.
However, when you need rich, detailed insights about every device—configs, software, and more—active discovery steps up, especially with credentials in hand.
For most IT teams, the smartest move is the hybrid approach. It combines passive’s subtlety with active’s depth, giving you comprehensive visibility without straining your network.
Here’s on the go:
- When your priority is zero network impact → go passive.
- But when the goal is deep configuration data → go active (with credentials).
- However, need something in between–comprehensiveness yet with minimal risk → go hybrid.
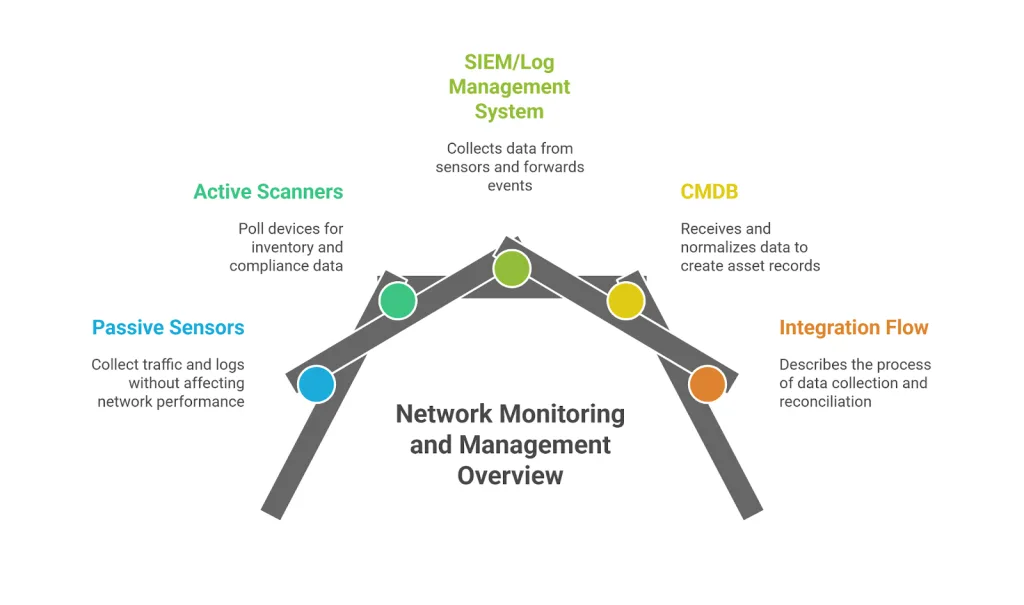
Implementation basics for IT asset discovery
TL;DR: Successful asset discovery balances network safety, data completeness, and IT operational efficiency using proven best practices for scan scheduling, sensor placement, credential handling, and performance metrics.
Implementing IT asset discovery, whether active, passive, or hybrid, requires deliberate planning and ongoing management. Below are practical best practices distilled from industry leaders and emerging standards to ensure your discovery program is effective, safe, and scalable.
Scheduling active scans
- Choose off-peak or maintenance windows. Run active scans when network traffic is lowest (typically nights or weekends) to minimize impact on business-critical systems.
- Break large networks into subnets. Instead of scanning the entire network at once, segment scans by subnet or location to reduce bandwidth spikes and avoid ping storms.
- Throttle scan traffic. Use vendor tools that support traffic shaping or scanning rate controls to prevent congestion or packet loss.
- Coordinate with change management. Align scan schedules with IT and OT maintenance windows to avoid false alerts and operational conflicts.
Passive sensor placement
- Deploy at strategic aggregation points. Install passive sensors at network chokepoints such as core switches, data center aggregation layers, and cloud edge gateways to maximize traffic visibility.
- Cover critical and sensitive segments. Include operational technology (OT) networks, cloud connectors, and remote access points to detect hidden or fragile devices.
- Validate sensor coverage regularly. Use flow analytics and traffic monitoring to ensure all expected network segments are monitored, adjusting sensor placement as network topologies evolve.
Credential management
- Use read-only access. Configure credentials with the least privilege necessary to gather detailed asset information while reducing security risks.
- Store credentials securely. Utilize credential vaults or secure password managers with audit logging to protect and rotate credentials regularly.
- Tier credentials by asset type. Apply more restrictive credentials for sensitive systems and elevated access where deep scans of complex devices are required.
Change windows & coordination
- Communicate the scan impact and timelines. Proactively inform IT, OT, and business teams about scheduled scans to prevent surprises and ensure cooperation.
- Integrate with IT Service Management (ITSM) tools. Incorporate discovery scan schedules into ITSM calendars and incident management workflows for disciplined operations.
Success metrics & KPIs
Measure and track the following regularly to validate and improve your asset discovery program:
- Asset coverage (%). Portion of total expected devices identified and inventoried; benchmark improvements over time.
- Mean time to inventory (MTTI). Average time from device introduction to detection and inclusion in inventory.
- CMDB accuracy. Reduction in stale or unknown configuration items (CIs) through discovery-driven enrichment.
- Unknown device reduction. Decrease in unrecognized or unmanaged endpoints visible on the network.
Here’s something toast from first-hand experience:
| Real-world scenarios of active and passive discoveryRemote workforce laptop returns online When a remote employee’s laptop reconnects to the corporate network after a period offline, passive discovery first detects this device non-intrusively through DHCP logs and syslog events generated during VPN connection. This instant detection helps asset managers maintain real-time awareness without deploying active probes that might slow the connection or disrupt workflows. Following initial detection, active discovery performs credentialed scans or agent queries when the device is reachable, enriching the asset inventory with operating system version, installed patches, and configuration insights. This two-phase process reduces the time to inventory dramatically and improves data accuracy. OT production line monitoring Industrial environments rely on continuous operation with minimal interruptions, making discovery challenging. In such settings, passive discovery sensors monitor network flows and device logs continuously, ensuring asset visibility without causing disruptions. Because active scans risk affecting PLCs, SCADA systems, and other sensitive equipment, credentialed or agent-based active discovery is restricted to carefully scheduled maintenance windows. This segmentation protects production uptime while ensuring critical firmware or patch updates are reflected in the CMDB. |
Unlock complete IT asset visibility with Virima’s proven best practices
Virima’s industry-leading IT asset discovery approach combines deep technical expertise with practical guidance honed through working with complex enterprise and hybrid-cloud environments.
Here are the key best practices that set Virima apart:
Recommended sensor placement
- Deploy passive sensors strategically at network chokepoints, including core switches, data center aggregation layers, cloud ingress/egress points, and VPN concentrators to maximize traffic visibility across all segments.
- Supplement with active, credentialed scans targeting critical asset pools like Windows and Linux servers, databases, and OT/ICS devices during approved maintenance periods to avoid service disruption.
- Extend discovery reach with agent-based monitoring on remote or disconnected devices that don’t routinely communicate on the corporate network.
Ideal scan schedule by asset class
- Core infrastructure (servers, network gear). Frequent active scans (daily or weekly) maintain detailed, real-time inventory and vulnerability posture.
- Virtual/cloud assets. Continuous passive monitoring enhanced with cloud APIs combined with weekly active reconciliation, ensures growing cloud footprints stay visible and governed.
- Remote workforce endpoints. Passive discovery on arrival with periodic active scans scheduled off-hours minimizes impact on users.
- OT/ICS environments. Passive-only baseline monitoring with quarterly or event-driven active scans respects operational fragility without exposing production risk.
Credential tiering
- Always use read-only access with the least permissions needed for scanning to reduce security risks.
- Grant higher-level credentials only for devices that require more detailed checks like patch updates or configuration audits.
- Store credentials safely in secure vaults that track access and rotate passwords regularly to maintain strict security controls.
- This simple approach helps you get full visibility while keeping your network safe and running smoothly.
Simplified coverage model
Virima recommends a pragmatic hybrid ratio to balance visibility and operational impact:
| 60% Passive Baseline + 40% Targeted Active Scans⇒ 95% Asset Visibility60% Passive Baseline + 40% Targeted Active Scans⇒ 95% Asset Visibility |
This model delivers robust foundational detection with continuous passive listening while enriching critical assets and unknowns with deeper active assessment.
Empirical customer feedback shows improved time-to-inventory and CMDB accuracy while preserving network stability.
Risk-based prioritization formula for discovery
To optimize resources and prioritize discovery efforts, Virima advises using a prioritization formula that weighs:
| Priority Score=Visibility Gap×Business Criticality×Threat ExposurePriority Score=Visibility Gap×Business Criticality×Threat Exposure |
Where:
- Visibility gap: Degree of unknown or outdated information on an asset or segment.
- Business criticality: Impact of the asset on key business functions or compliance.
- Threat exposure: Likelihood and potential damage from vulnerabilities or attacks targeting the asset type.
This formula ensures discovery cadence and depth are allocated where the risk-return ratio is highest, focusing attention on devices that pose the greatest security or operational risks if left unmanaged.
Through this combination of strategic sensor placement, adaptive scan scheduling, credential controls, and risk-prioritized focus, Virima assists organizations in building confident, comprehensive, and continuously updated IT asset inventories that bolster security and operational compliance.
Identifying vulnerabilities and maintaining visibility
Combining active and passive approaches helps identify vulnerabilities across both connected and previously unseen devices. Active methods pinpoint configuration flaws and unpatched systems, while passive monitoring ensures ongoing visibility of devices that don’t respond to direct queries.
This hybrid approach ensures complete asset coverage across your network, including IoT, cloud, and on-premises environments.
Takeaway: Master IT asset discovery for unmatched visibility and control
Effective IT asset discovery is the cornerstone of infrastructure security, operational efficiency, and compliance readiness. Whether you prioritize zero network disruption with passive methods, need deep configuration insight from active scans, or seek the best of both worlds with discovery for hybrid IT, the right approach enables you to:
- Identify and inventory all assets accurately
- Reduce unknown and unmanaged devices significantly
- Ensure timely updates to your CMDB for audit and governance
- Minimize impact on critical or fragile systems
Virima’s proven best practices—strategic sensor placement, adaptive scan cadence, and risk-based prioritization help you achieve up to 95% complete, real-time asset visibility with minimal disruption.
Ready to elevate your IT asset management?
See a hybrid discovery demo to experience Virima’s comprehensive solution.
Schedule now!